In today’s digital landscape, the evolution of cyber security marketing strategies has become a focal point for B2B and B2G marketing leaders. As cyber threats grow increasingly sophisticated, the demand for robust cybersecurity solutions has surged. This dynamic environment presents unique challenges and opportunities for marketers aiming to differentiate their offerings and communicate effectively with decision-makers. Understanding the nuances of cyber security marketing is essential for staying competitive and ensuring that businesses are well-protected against potential threats.
Adapting to the Changing Threat Landscape
The cyber threat landscape is continuously evolving, with new vulnerabilities and attack vectors emerging regularly. This necessitates a proactive approach to cyber security marketing. Marketers must stay ahead of trends and provide relevant, timely information to potential clients. Educating audiences on the latest threats and how specific solutions can mitigate these risks is crucial. By doing so, marketers can position their brands as thought leaders and trusted partners in cybersecurity.
Leveraging Data-Driven Insights
Data-driven marketing is no longer optional in the cybersecurity sector. With vast amounts of data generated daily, marketers have the opportunity to harness these insights to tailor their campaigns. Understanding customer behavior, preferences, and pain points allows for more personalized and effective marketing strategies. Utilizing analytics tools can help marketers identify trends, measure campaign performance, and optimize efforts for better engagement and conversion rates.

Learn how we helped leader cyber firm SonicWall cut through the noise
Building Trust Through Transparency
Trust is a cornerstone of successful cyber security marketing. In a field where credibility is paramount, transparency in communication is essential. Companies must clearly articulate their security protocols, privacy policies, and compliance with industry standards. Providing case studies, whitepapers, and testimonials can further establish trust and credibility. Clients need assurance that their data and systems are in safe hands, and transparent marketing efforts can reinforce this confidence.
Integrating Multi-Channel Strategies
Effective cyber security marketing strategies require a multi-channel approach. With diverse audiences across different platforms, marketers must leverage various channels to maximize reach and impact. This includes digital advertising, social media, content marketing, and events. By aligning these channels with a cohesive message, marketers can enhance brand visibility and foster deeper connections with potential clients. Understanding the preferences and behaviors of target audiences on each platform is key to crafting tailored messages that resonate.
The Role of Thought Leadership
In the competitive cyber security market, thought leadership can be a powerful differentiator. By sharing expert insights, predictions, and analyses, companies can position themselves as industry leaders. This not only builds brand authority but also attracts potential clients seeking reliable partners. Thought leadership can be demonstrated through blogs, webinars, speaking engagements, and media appearances, providing valuable content that addresses the industry’s most pressing challenges.
Emphasizing User Experience
As with any industry, user experience (UX) plays a critical role in cyber security marketing. Ensuring that digital touchpoints, such as websites and applications, are user-friendly and informative can significantly impact client perceptions. A seamless and intuitive UX can enhance customer satisfaction and foster loyalty. Marketers must collaborate with UX designers to create engaging interfaces that effectively communicate complex cybersecurity concepts.

Check out how Bluetext revolutionized Security Scorecard’s website
Fostering Collaboration with Stakeholders
Collaboration between marketing and cybersecurity teams is vital for crafting effective strategies. By working closely with IT and security professionals, marketers can gain deeper insights into the technical aspects of their offerings. This collaboration ensures that marketing messages are accurate, relevant, and resonate with technical and non-technical audiences alike. Cross-departmental teamwork can also lead to innovative solutions and campaigns that address the nuanced needs of clients.
Exploring Innovative Technologies
The integration of innovative technologies, such as artificial intelligence and machine learning, is transforming cyber security marketing. These technologies can enhance threat detection, automate responses, and provide predictive analytics. Marketers can leverage these advancements to showcase cutting-edge solutions and demonstrate their company’s commitment to innovation. Highlighting the use of advanced technologies can appeal to tech-savvy clients and set a brand apart from competitors.
Partnering with Experts
As cyber security marketing strategies continue to evolve, partnering with a knowledgeable marketing agency can provide a competitive edge. Bluetext, a leading cybersecurity marketing agency, offers expertise in crafting strategies that resonate with B2B and B2G audiences. By understanding the intricacies of the cyber landscape and leveraging data-driven insights, Bluetext helps businesses effectively communicate their value propositions and build lasting relationships with clients. For tailored strategies and expert guidance, contact Bluetext today.
As digital transformation continues to reshape industries, the future of website design and development is increasingly critical for B2B and B2G organizations. In today’s fast-paced digital landscape, a company’s website is not just a digital storefront but a powerful tool for engagement, conversion, and growth. For marketing leaders, understanding the evolving trends in website design and development is essential to staying competitive. This blog explores the future of web development and what B2B and B2G organizations need to know to remain at the forefront.
Embracing Responsive and Adaptive Design
The need for responsive and adaptive design has never been more pressing. With a growing number of users accessing websites via mobile devices, B2B and B2G companies must ensure their websites are fully optimized for all screen sizes. Responsive design ensures that a website’s layout automatically adjusts based on the user’s device, while adaptive design offers different layouts for different devices. These approaches improve user experience and increase engagement and conversion rates.
For organizations looking to optimize their digital presence, partnering with a leading website design agency can provide the expertise needed to implement these design strategies effectively.

Check out how we unified BigBear.ai’s brand identity
Integration of AI and Machine Learning
Artificial intelligence (AI) and machine learning are revolutionizing website design and development. These technologies enable personalization at scale, allowing websites to offer tailored content and experiences to individual users. AI-driven chatbots, predictive analytics, and dynamic content are becoming standard features that enhance user interaction and satisfaction.
B2B and B2G companies should consider integrating AI tools to analyze user behavior, predict future trends, and deliver a more customized experience. By leveraging these technologies, organizations can stay ahead of the competition and meet the ever-changing expectations of their audiences.
Prioritizing Website Security
With cyber threats on the rise, website security is a top priority for B2B and B2G entities. Secure Socket Layer (SSL) certificates, two-factor authentication, and regular security audits are essential components of a robust security strategy. Moreover, with increasing regulations such as GDPR, organizations must ensure compliance to avoid legal repercussions and build trust with their users.
Engaging with a specialized cybersecurity marketing agency can help organizations develop a comprehensive security framework that protects both the company and its clients.
The Rise of No-Code and Low-Code Platforms
No-code and low-code platforms are democratizing website development, allowing non-technical users to create and manage websites without extensive coding knowledge. These platforms accelerate the development process and reduce costs, making them attractive options for many B2B and B2G organizations.
While these platforms offer significant advantages, it’s crucial to evaluate their limitations and ensure they meet the specific needs of your organization. Collaborating with a professional Drupal development agency can provide the necessary expertise to balance ease of use with advanced functionality.
Dig into the work that helped Noblis own their space
Focusing on Accessibility and Inclusivity
Accessibility and inclusivity in web design are no longer optional; they are essential. Websites must be designed to accommodate users with disabilities, ensuring that all users have equal access to information and services. This includes implementing features such as screen reader compatibility, keyboard navigation, and text-to-speech options.
By prioritizing accessibility, B2B and B2G companies not only comply with legal requirements but also expand their audience reach. Engaging with an agency that understands the nuances of website localization and multilingual support can further enhance inclusivity and global reach.
The Importance of User Experience (UX) Design
User experience design is at the heart of successful website development. A well-designed UX can significantly impact user satisfaction and retention. This involves understanding user behavior, creating intuitive navigation, and ensuring fast load times.
For B2B and B2G organizations, investing in UX design translates into better engagement and higher conversion rates. Collaborating with a DC interactive web design firm can help refine the user experience, ensuring that websites are both functional and enjoyable to use.
Bluetext’s View
The future of website design and development is dynamic and filled with opportunities for innovation. B2B and B2G organizations that stay ahead of these trends will enhance their digital presence and drive business success. As technology continues to evolve, so too must the strategies employed by marketing leaders. For those looking to leverage the latest in design and development, partnering with experts is key. Contact Bluetext to explore how our strategic insights, branding expertise, and campaign support can elevate your organization’s digital strategy.
Public sector messaging is undergoing a transformation. The move to digital services, the rise of AI, an urgent push for cybersecurity, and growing expectations for transparency have changed how agencies communicate with citizens, industry partners, and internal stakeholders. In this climate, advertising agencies in Washington DC have become pivotal. They are translating complex policy goals into clear, measurable narratives that build trust and drive action across federal, state, and local audiences. For marketing leaders in B2B and B2G, understanding how these firms operate is essential for shaping strategies that resonate in a high-stakes, highly scrutinized environment.
Why the Capital Region Sets the Pace for Public Sector Marketing
Advertising agencies in Washington DC sit at the intersection of policy, procurement, and public perception. Proximity to decision makers matters because insights from Capitol Hill, federal agencies, think tanks, and contractors flow quickly into messaging strategy. The best advertising agencies in Washington DC leverage this access to anticipate shifts in budgets, compliance mandates, and citizen priorities before they hit the broader market.
Unlike traditional commercial campaigns, public sector communications must satisfy multiple constituencies at once. Leaders need language that aligns to legislative directives, speaks credibly to technical evaluators, and translates into accessible citizen experiences. Advertising agencies in Washington DC are uniquely adept at aligning these priorities, because they collaborate daily with legal, policy, and program offices alongside creative, media, and analytics teams.
For brands operating in the federal ecosystem, this context is not a nice-to-have. It is the difference between campaigns that are compliant yet forgettable and campaigns that are compliant and effective. That is why many enterprises and contractors partner with a DC advertising agency to ensure every message respects the process while still breaking through.
What Distinguishes Top Agencies Serving the Public Sector
Executive audiences often ask what sets advertising agencies in Washington DC apart from peers in other markets. Three qualities stand out. First is a deep literacy in procurement and acquisition models. Teams understand how communications support the full capture lifecycle, from market research to RFI to recompete. Second is fluency in mission language. Agencies know how to elevate outcomes like readiness, resilience, access, and equity without drifting into jargon. Third is a disciplined approach to risk. Advertising agencies in Washington DC build safeguards that respect appropriations rules, the Paperwork Reduction Act, Section 508, and privacy requirements while enabling modern creative and paid media.
These capabilities translate into superior orchestration. The better the grasp of stakeholders and statutes, the freer the creative team becomes to deliver powerfully simple stories. Advertising agencies in Washington DC ensure creative excellence is never decoupled from mission fidelity.
The highest performers also invest in strong partnerships across public affairs, program leads, and integrator teams. That collaboration speeds approvals and compresses timelines, a major advantage when announcements, policy windows, or budget cycles demand rapid response.
How Agencies Build Evidence-Based Messaging Frameworks
Public sector communication succeeds when every claim is traceable, defensible, and relevant to mission outcomes. That begins with research. Leading advertising agencies in Washington DC conduct structured stakeholder interviews, social listening, and voice-of-the-customer studies to surface real needs and barriers. They map procurement influencers and technical validators to avoid over-indexing on a single persona.
From there, teams develop a clear hierarchy of messaging: top-line narrative, mission and market proof points, and technical substantiation. This process ensures a single source of truth that can flex from federal CIO briefings to program-level landing pages and social posts. When a brand needs to evolve its foundation, proven partners provide a rigorous messaging and positioning engagement that delivers clarity and consistency across every channel.
Advertising agencies in Washington DC also pressure-test messages for plain language standards, accessibility, and inclusivity. The result is content that reads easily for citizens, yet satisfies experts who look for specificity. This dual-read approach allows communications to move seamlessly between public and policymaker audiences.
Omnichannel Strategies That Reach Decision Makers and Citizens
Federal audiences consume information differently than commercial buyers. They attend briefings, review technical documentation, and rely on earned media and trusted associations. Advertising agencies in Washington DC know how to orchestrate an omnichannel plan that places the right content in each context without diluting the core message.
Winning plans often combine targeted paid media on professional platforms, high-value content for search capture, tailored email sequences for industry partners, and video explainers for citizen education. Many initiatives also include thought leadership and program microsites to centralize resources. Skilled advertising agencies in Washington DC ensure channel roles are clear, budgets are prioritized by influence, and handoffs are tracked between awareness, consideration, and action.
For B2G brands and contractors, the same rigor applies. Teams create compliant capture support and digital nurture paths, then align assets across conference cycles and contracting milestones. When you work with B2G content and digital marketing experts, your programs move in lockstep with agency priorities and procurement calendars.

Creative That Inspires Within Policy Boundaries
Contrary to popular belief, constraints can unlock better ideas. Advertising agencies in Washington DC excel at turning rules into creative guardrails that sharpen the work. Mission-forward storytelling, empathetic visuals, and precise language often outperform splashy concepts when trust and credibility are on the line. Leaders must communicate urgency without sensationalism, innovation without overpromising, and outcomes without political coloration.
When an initiative requires cinematic storytelling or a high-impact launch, the right partner can still deliver. The key is a creative process that engages legal, privacy, and program teams early and iterates toward solutions that meet standards. Advertising agencies in Washington DC use modular frameworks that adapt quickly as guidance evolves, so momentum never stalls.
Measurement and Accountability Tailored to Government Goals
Public sector KPIs look different than consumer metrics. The aim might be program enrollment, partner engagement, FOIA burden reduction, or adoption of digital self-service. Advertising agencies in Washington DC design analytics architectures that map marketing inputs to mission outcomes, from reducing call-center load to increasing qualified industry conversations ahead of an RFP.
Dashboards highlight channel effectiveness, message resonance, and audience lift over time. Advertising agencies in Washington DC also align reporting frequency and format to government cadence so program offices can integrate insights into performance reviews and budget justifications.
Emerging Trends Reshaping Public Sector Messaging
AI and Personalization With Guardrails
AI is enabling scale without sacrificing quality. Predictive analytics inform content prioritization, while responsible automation accelerates production. Advertising agencies in Washington DC deploy AI to identify message themes that correlate with action and to personalize experiences for role, mission, or geography. Crucially, they implement governance to protect privacy and keep human oversight central.
Accessibility and Multilingual Reach as Strategy
Accessibility is now a strategic imperative, not a compliance checklist. Section 508, plain language, and inclusive design practices drive higher engagement from every audience. Leading advertising agencies in Washington DC also help agencies expand multilingual content, ensuring communities receive accurate information in formats they trust. This improves service equity and strengthens program outcomes.
Cybersecurity and Trust by Design
Every communication touchpoint is a trust opportunity. From domain hygiene to citizen data flows, trust is designed into modern campaigns. Advertising agencies in Washington DC partner with security teams to ensure landing pages, forms, and analytics scripts meet stringent standards, and to explain security controls in clear language that reassures users.

How to Choose the Right DC Partner for Public Sector Work
Selecting among advertising agencies in Washington DC requires more than a portfolio review. Ask how the team structures discovery with program leads, legal, privacy, and procurement. Probe how they translate mission context into creative criteria. Confirm that they treat accessibility, data governance, and measurement as core competencies rather than add-ons. Review examples of public sector marketing work to validate the approach across issues and audiences.
- Experience across B2G and B2B to connect agency needs with industry partner realities, a hallmark of top advertising agencies in Washington DC.
- Proven frameworks for narrative development, testing, and approvals that fit government cadence.
- Omnichannel planning that aligns with events, policy milestones, and contracting cycles.
- Analytics tied to mission outcomes with clear targets, not just impressions or clicks.
- Creative leadership that thrives inside compliance, turning constraints into distinctiveness.
Scalable Content Engines Built for Government and Industry
Public sector communication rarely ends with a single announcement. Programs require ongoing education, myth-busting, and partner enablement. Advertising agencies in Washington DC build content engines that deliver consistent value across long timelines. Editorial calendars layer explainer videos, FAQs, webinars, case vignettes, earned media, and SEO content to improve discoverability and comprehension.
For contractors and technology partners, the same engine supports pipeline growth and capture support. Content must speak to mission owners while proving technical depth to evaluators. Agencies orchestrate how-and-why storytelling so industry buyers and contracting officers find the right asset at the right time, no matter their level of expertise.
Search and Discoverability for Federal and Citizen Queries
Search behavior in government communications is specific and often intent-rich. Advertising agencies in Washington DC optimize for terms tied to policy guidance, funding mechanisms, and program names. They build content clusters that answer high-value questions concisely, then support those pages with multimedia designed for quick comprehension. Structured content and clean information architecture help users navigate quickly between overview, technical detail, and action steps.
On the industry side, ads and organic content target evaluators who search for standards, certifications, and interoperability. Advertising agencies in Washington DC balance thought leadership with practical implementation guidance so technical teams trust what they read and can act on it.
Integrated Campaigns That Respect the Evaluation Process
In the federal environment, messaging often becomes part of the evaluation context even when not explicitly scored. That reality drives a premium on clarity, consistency, and verifiable claims. Advertising agencies in Washington DC help clients develop integrated campaigns that carry a single throughline from speaking points to landing pages to social and earned media. Every asset uses the same narrative scaffolding, so nothing contradicts or confuses.
This alignment reduces risk and increases velocity. It also makes content repurposing more efficient, a vital consideration when budgets must stretch across long deliberation cycles and overlapping initiatives.
Proven Processes That Move at the Speed of Policy
One hallmark of advertising agencies in Washington DC is the ability to pivot without sacrificing quality. As policy guidance shifts, teams refresh message maps and creative toolkits rapidly. Preapproved content modules, design systems, and editorial guardrails let programs adapt without rework. Agencies also run governance playbooks that accelerate legal and accessibility reviews, shortening time to market and protecting consistency at scale.
For leaders managing multiple initiatives, this operational discipline is as valuable as the creative itself. It keeps workstreams on schedule and protects program credibility when timelines are tight and scrutiny is high.
When to Invest in a Full Rebrand vs. a Campaign Refresh
Leaders frequently ask whether their program needs a rebrand or a focused campaign. Advertising agencies in Washington DC evaluate mission evolution, stakeholder confusion, and performance data to make that call. If the brand story no longer matches program reality, a strategic refresh is in order. If the core is sound but awareness or engagement is lagging, a campaign tailored to new priorities may deliver faster impact. Either path benefits from a rigorous foundation and a clear creative idea supported by executional detail.
How Bluetext Helps Public Sector Leaders Win Hearts, Minds, and Metrics
As a partner to agencies, associations, and contractors, Bluetext brings the integrated strategy, creative, and analytics discipline that modern public sector work requires. Our teams have built mission-forward narratives, omnichannel plans, and accessible digital experiences that scale. For enterprise and B2G brands entering or expanding in the federal space, we align capture needs, partner enablement, and message governance so go-to-market stays streamlined and effective.
When your organization needs a full strategic reset, Bluetext delivers with proven frameworks and dedicated experts who design for both speed and rigor. To see the breadth of creative impact we can deliver, explore our advertising portfolio and imagine how a sharper story could elevate your next initiative.
The Bottom Line for Executive Marketers
The difference between a compliant message and a compelling message is not semantics. It is strategy, empathy, and operational excellence. Advertising agencies in Washington DC combine mission fluency with creative precision to help programs and partners communicate clearly, credibly, and at scale. They understand how narratives travel through policy windows and budget cycles and how to measure progress in terms that matter to leaders and citizens.
For executive teams planning the next fiscal year or preparing a major initiative, now is the time to pressure-test your narrative, refresh your channel strategy, and tighten your measurement architecture. Partner with an agency that treats your mission as its north star. Bluetext is ready to help you define your story, architect your omnichannel plan, and activate campaigns that move metrics and inspire action. Explore our capabilities and contact us to start shaping public sector messaging that earns trust and delivers results with the strength and sophistication you expect from advertising agencies in Washington DC.
Public sector leaders face an expectations gap. Constituents, businesses, and partner agencies expect personalized, transparent, and secure experiences that match the best of the private sector. Budgets, procurement, and regulatory constraints rarely make that simple. This is where brand strategy agencies step in. By fusing research, policy awareness, design systems, and measurable activation, these partners are redefining how agencies, authorities, and government contractors express mission, build trust, and drive engagement. For executive teams tasked with modernizing programs and attracting talent or investment, understanding what brand strategy agencies do and how they do it can be the difference between incremental change and meaningful transformation.
Why Public Sector Branding Demands a Different Playbook
Brand strategy agencies that work in the public sector understand that reputations are earned over long cycles, in complex stakeholder environments, and under constant public scrutiny. The brand is not only a promise but an operational framework for delivering equitable, accessible, and secure services. Unlike commercial rebrands that prioritize rapid market share, public sector branding must reconcile policy, mission, and accountability with modern usability and credible storytelling.
Brand strategy agencies navigate requirements like Section 508 accessibility, records retention, and chain-of-custody communications while still producing compelling creative. They translate legislation and program charters into simple narratives that a resident, a Hill staffer, and a systems integrator can each understand. That is not a cosmetic exercise. It is a strategic discipline that moves a mission forward.

Invictus needed a brand that could scale. We built it.
What Do Brand Strategy Agencies Bring to Government and Quasi-Government Brands?
Brand strategy agencies bring the rigor of management consulting together with the agility of modern design and content practices. The result is a brand system that works from policy memo to website hero, from community briefing to trade show booth. The value shows up in four core areas.
Research That Reflects Reality and Builds Alignment
Brand strategy agencies invest in interviews, listening sessions, message testing, and competitive audits that respect the public record. By combining stakeholder interviews with sentiment analysis, they ensure the brand is grounded in facts and real-world perceptions. This creates alignment across political leadership, career civil servants, and external partners before creative decisions even start.
Messaging Architecture That Balances Mission and Outcomes
Brand strategy agencies craft narrative frameworks that connect mission, program outcomes, and citizen benefits in a hierarchy that works across channels. A strong messaging backbone clarifies what to say in a grant announcement, how to position a research program, or how to explain a cross-agency initiative in one page. For a deeper look at how this comes together in practice, explore Bluetext’s approach to messaging and positioning.
Visual Systems Built for Accessibility and Scale
Brand strategy agencies create visual identities that scale to thousands of pages, dozens of social channels, and many field teams. Color, typography, iconography, and photography choices must pass accessibility checks while remaining distinct and memorable. Templates and component libraries enable consistent execution whether a designer is in-house, at a contractor, or within an affiliated authority.
How Digital Trust and Cybersecurity Influence Brand Architecture
Trust is now the primary economic currency of public sector engagement. Brand strategy agencies integrate digital trust principles into brand architecture by aligning identity decisions with privacy policies, cyber posture, and data governance. That integration shows up in how a site handles consent, how a campaign promises data use, and how visual cues signal security without creating fear.
In an era of phishing and misinformation, brand strategy agencies audit the entire digital estate for consistency, appropriate use of seals and marks, and clear calls to action. They equip internal teams with playbooks that reduce risk. The result is a brand that reads as reliable because the experience is coherent, safe, and respectful of citizen data.

View the strategy behind Mantech’s brand transformation
How Brand Strategy Agencies Modernize Legacy Programs Without Losing Mission
Legacy brands often carry deep reservoirs of trust but struggle with fragmented visuals and outdated language. Brand strategy agencies diagnose which signals of continuity to retain and which components to modernize. That could mean preserving a seal while updating a wordmark, or keeping a recognizable tagline while evolving the narrative to emphasize outcomes and inclusion.
For federal contractors and state partners, brand strategy agencies also orchestrate co-branding frameworks that respect procurement rules and align with partner guidelines. The discipline prevents brand dilution and reduces review cycle time. Agencies that get this right shorten the path from idea to impact, especially when legislative or budget windows are tight.
What Metrics Matter for Public Sector Brand Performance
Executives need a pragmatic dashboard that moves beyond vanity metrics. Brand strategy agencies define and track indicators tied to mission and stakeholder behavior. Common metrics include:
- Message comprehension and recall across priority audiences
- Accessibility scores, task completion, and time to information on digital properties
- Trust and favorability measures among constituents and partners
- Application, enrollment, or participation rates for key programs
- Talent pipeline indicators, including qualified applicants for hard-to-fill roles
- Cost per qualified engagement for campaigns that drive public action
Brand strategy agencies use these metrics to calibrate creative, content, and media allocation. They also establish governance so insights flow back to leadership and inform policy communications, not only marketing outputs.
How AI and Data Are Reshaping Public Sector Brand Strategy
AI is changing the cadence of insight and execution. Brand strategy agencies deploy privacy-conscious methods to surface audience questions, simplify content, and test variations at scale. The goal is not automation for its own sake. The goal is clarity, speed to value, and compliance. Modern content operations pair human editorial oversight with AI-enabled taxonomy, entity recognition, and accessibility checks. The result is accurate, readable content that reaches people the first time they look for it.
Data-enabled brand governance also makes it possible to show which narratives drive trust and participation versus those that only generate clicks. Brand strategy agencies operationalize this feedback loop in editorial calendars, asset libraries, and training modules so every team communicates with consistency and purpose.
Procurement-Friendly Ways to Engage an Agency Partner
Working with brand strategy agencies does not require a complex megaphone contract from day one. Many public sector leaders start with a discovery sprint, a messaging workshop, or a visual refresh pilot. From there, they scale into content systems, digital experience design, and campaign activation. Phased scopes mirror the decision-making cadence of public organizations and create value early.
Brand strategy agencies also help structure documentation that supports budget requests and RFP development. A clear current-state analysis and future-state roadmap simplify vendor management and accelerate approvals. This disciplined approach keeps brand modernization on schedule even when leadership or legislative priorities evolve.
Case-Inspired Patterns That Work Across the Public Sector
Brand strategy agencies have seen what works across agencies, authorities, and government-adjacent organizations. Several patterns consistently deliver results:
- Mission-first messaging that translates policy into human outcomes
- Design systems that hard-code accessibility and provide flexible components
- Journey maps that connect awareness to action and reduce friction for citizens
- Training and governance frameworks that build internal capacity and continuity
- Measurement that ties storytelling to service delivery and talent attraction
To see how these elements come together in complex environments, review Bluetext’s public sector work and explore how narrative, visual systems, and digital experiences align to drive adoption and trust.
Pull back the curtain on Kratos’s brand transformation
How Brand Architecture Supports Cross-Agency Collaboration
Shared missions often require shared narratives. Brand strategy agencies build brand architecture that clarifies parent-child relationships, co-sponsorship guidelines, and naming for pilots or working groups. This structure reduces duplication, streamlines approvals, and prevents confusing overlaps when programs migrate or expand.
When a state agency collaborates with a federal initiative or a university consortium, brand strategy agencies create co-branding rules that maintain legal integrity while communicating a unified purpose. The audience sees one mission and one path to action, even if multiple partners are at work behind the scenes.
From Narrative to Experience: Closing the Loop in Digital
Modern constituent journeys begin in search, unfold on mobile, and conclude across channels. Brand strategy agencies align content design, IA, and performance SEO so the brand shows up where people actually look for information. They prioritize plain language, logical pathways, and structured data so that FAQs, forms, and eligibility criteria are easy to find and understand.
That same discipline extends to campaigns. Brand strategy agencies engineer landing pages, onboarding flows, and feedback loops that turn intent into completion. For inspiration on how identity and experience design connect, explore Bluetext’s portfolio of branding programs that integrate strategy with digital execution.
The Role of Storytelling in Policy Communication
Complex policy needs narrative, not spin. Brand strategy agencies transform technical language into stories about community impact, safety, resilience, and opportunity. These narratives help leaders explain trade-offs, invite collaboration, and show progress without overselling. They also equip spokespeople and program managers with consistent talking points that stand up under scrutiny.
When paired with well-designed visuals and data storytelling, these narratives turn dense reports into content people share and reference. That momentum improves the quality of dialogue between agencies, lawmakers, and the public.
Common Pitfalls Brand Strategy Agencies Help Avoid
Public sector transformations rarely fail because of a single decision. They stall when teams attempt to fix everything at once, overlook governance, or confuse internal enthusiasm with external clarity. Brand strategy agencies de-risk change by sequencing work, codifying standards, and validating messages with real audiences early. They also protect teams from scope creep by documenting principles and decision rights that hold up during leadership changes.
Another frequent pitfall is misaligning brand with recruiting. Brand strategy agencies convert mission language into a talent value proposition that appeals to engineers, analysts, and operators who could work anywhere. Clear EVP messaging shortens time to hire and lifts acceptance rates for priority roles.
Selecting the Right Partner for Your Mission
Choosing among brand strategy agencies requires criteria that look beyond portfolios. Evaluate partners on their ability to synthesize research into strategy, their fluency with public sector constraints, and their track record building systems that scale. Ask how they measure brand performance and how they enable your team to sustain the change. Look for a right-sized approach to discovery and a plan for rapid wins that build momentum.
Examine collaboration habits as well. Brand strategy agencies should integrate with policy, legal, IT, and communications, not only with marketing. They should speak the language of procurement and offer artifacts your organization can use immediately, such as message maps, design libraries, and training assets.
Why Bluetext for Public Sector Branding
Bluetext is a partner to leaders who need brand strategy that respects mission and delivers measurable outcomes. Our teams bring cross-disciplinary expertise that blends research, narrative, design, and activation. We understand the realities of government, from accessibility to approval workflows, and we design programs that adapt. Explore our perspective on brand strategy agencies and how the discipline is evolving to meet the needs of public organizations and the contractors that support them.
For agencies, associations, and integrators operating at the intersection of policy and technology, Bluetext develops systems that connect the dots. Our approach integrates strategy and creative with activation across content, search, and media. To understand the breadth of our capabilities in regulated and mission-driven industries, visit our public sector work and see how brand modernization moves from insight to implementation.
Practical Next Steps to Start Your Transformation
Successful change begins with focused action. Brand strategy agencies often recommend one or more of the following starting points:
- Message and narrative audit that clarifies strengths, gaps, and priorities
- Visual system refresh aligned to accessibility and contemporary use cases
- Stakeholder workshop to align leadership on purpose, proof, and priorities
- Content and IA blueprint that improves findability and task completion
- Campaign framework that drives a single, high-impact behavior
Each step generates assets your team can use right away, while building a foundation for a full transformation. Brand strategy agencies structure these initiatives to fit budget cycles and oversight requirements, which keeps momentum strong and measurable.
Connecting Brand Strategy to Growth in the B2G Ecosystem
Government contractors live in a hybrid world of commercial expectations and public accountability. Brand strategy agencies help contractors articulate differentiated value to program managers, contracting officers, and end users. Clear positioning improves win rates and accelerates teaming decisions. For organizations ready to expand their presence, partnering with seasoned public sector experts reduces brand risk and improves capture effectiveness across pursuits.
Brand strategy agencies also align brand with analyst relations, media, and trade show investments. Unified messages and systems create compounding effects across channels, which shows up in pipeline quality and the speed of stakeholder education.
The Path Forward
Public sector expectations are rising. Mission complexity is increasing. Budgets remain under pressure. Brand strategy is no longer a veneer but a core capability that aligns policy, service, and stakeholder experience. Brand strategy agencies provide the frameworks, assets, and training to make that capability operational. When leaders invest in this discipline, they unlock clarity, trust, and measurable progress that endures beyond a single campaign or administration.
If your organization is ready to clarify its mission, modernize its identity, and engage the audiences that matter, the next step is a conversation. Reach out to contact Bluetext to discuss how our team can help you plan, build, and activate a brand platform that advances your goals with speed and certainty.
Cyber threats are escalating in speed, scale, and sophistication, and the buying committee is expanding just as quickly. That reality raises the bar for marketing leaders in security. Winning requires relevance to CISOs, clarity for practitioners, and credibility with the board. Working with a cybersecurity marketing firm that understands both the technology and the enterprise sale is the difference between incremental results and market leadership. The following insights distill what leading firms are doing right so you can elevate strategy, accelerate pipeline, and strengthen brand authority.
What separates top cybersecurity marketing partners today
The best programs begin with an unflinching focus on the audience reality. A high-performing cybersecurity marketing firm internalizes how risk, compliance, architecture, and budget decisions are actually made. That means moving from feature-first messaging to evidence-led value narratives tied to operational outcomes like mean time to detect, dwell time reduction, and policy enforcement at scale. The firm’s job is to translate deep technical differentiation into stories that de-risk the decision for executives while equipping champions to drive consensus.
- Precision positioning rooted in market structure. Leading teams map competitors, substitutes, and adjacencies to carve out a defensible lane. A cybersecurity marketing firm then defines proof points and customer language that neutralize “good enough” alternatives.
- Program architecture aligned to the full buying committee. Security engineers want hands-on depth, finance leaders want cost predictability, and agencies require compliance clarity. A single plan must satisfy all without diluting the core idea.
- Relentless emphasis on credibility. Analyst relations, third-party validations, and quantified case studies are nonnegotiable. Trust is earned through substance and consistency.
How to craft a category narrative that buyers and analysts remember
A category narrative should make complex concepts immediately graspable. The goal is not to describe everything your platform does. The goal is to frame the problem and your point of view so succinctly that buyers can retell it inside their organizations. A seasoned cybersecurity marketing firm builds a narrative that aligns to pain, risk, and urgency across three tiers: macro threats, organizational impact, and role-based priorities. Done well, this narrative becomes the spine for campaigns, content, and sales tools.
Message architecture that scales across roles and channels
Start with a one-sentence promise that is anchored to a measurable outcome. Support it with three pillars that connect to platform capabilities and use cases. Translate each pillar into executive, practitioner, and partner proof points. A cybersecurity marketing firm then operationalizes the architecture across website pages, enablement decks, demo scripts, and PR talking points to maintain signal consistency while allowing depth where needed.
Which channels deliver pipeline in cybersecurity right now
Security buyers need a reason to reallocate constrained budgets. That means showing proof early, not after the gated form. ABM and field marketing work when they provide value in the first interaction. A high-performing cybersecurity marketing firm leans into technical content, peer validation, and tactical tools that help teams move an initiative forward this quarter. Events, communities, and intelligence briefings continue to convert when they are built around practitioner utility rather than product promotion.
Paid, owned, and earned tactics calibrated for intent
Start by using search and review platforms to harvest late-stage demand and direct it toward differentiated assets. Bolster credibility with earned media on real issues such as SaaS misconfigurations, software supply chain risks, and OT exposure. On owned channels, invest in explainers, frameworks, and sample policies that practitioners can deploy immediately. A cybersecurity marketing firm should unify these threads through a simple conversion path that prioritizes demos, proofs of concept, and risk assessments tied to business outcomes.
How to market security solutions to the public sector without risk
Public sector innovation cycles and buying processes differ meaningfully from enterprise norms. Compliance, certifications, and mission alignment matter as much as features. A strong cybersecurity marketing firm knows how to position capabilities for federal, state, and local requirements while respecting rules around procurement-sensitive claims. It is critical to balance thought leadership with precise language that aligns to contract vehicles, cybersecurity frameworks, and zero trust mandates.
Map campaign themes to mission outcomes such as resilience, continuity of operations, and cross-agency collaboration. Translate technical claims into acquisition-ready language that references control families and policy directives without overstepping. For B2G programs, align messaging to role-specific triggers for CIO, CISO, and program executive stakeholders. A cybersecurity marketing firm will also synchronize content release cycles with budget timelines and period-of-performance realities to improve win probabilities.
Proof builds trust: assets that convert security skeptics
Security decision makers have learned to ignore marketing claims. Instead, they respond to proof they can interrogate. Anchor campaigns in artifacts that reflect the rigor of your program and the maturity of your customers. This is where a cybersecurity marketing firm can unlock disproportionate impact by shifting your content mix toward evidence and practitioner utility.
- Quantified customer outcomes. Build repeatable case study formats with before-and-after metrics like time to remediate and alert fatigue reduction.
- Technical validation. Commission red team exercises or third-party pen tests and publish summarized findings with sufficient technical fidelity.
- Economic framing. Translate risk and controls into financial terms, making it easier for CFOs to support the plan.
- Hands-on experiences. Host guided labs and simulations that replicate real attack paths and defensive workflows.
Video and interactive experiences that reduce time to conviction
Video is often the fastest route to comprehension when products span identity, data, and network layers. Create short explainers that visualize control points along the kill chain, then drive to a deeper interactive lab. An expert cybersecurity marketing firm will sequence formats for progressive discovery, starting with an animated overview, bridging to a narrated demo, and culminating in a hands-on challenge. This structure compresses time to conviction for technical buyers and simplifies storytelling for executives.

Check out our video work with SecurityScorecard
Search, content, and AEO strategies for technical audiences
Search behavior in cybersecurity is fragmented across roles and stages, which demands precision. Rather than chasing generic keywords, define intent clusters that reflect real jobs to be done, such as exposure management, least privilege, or secure software development. An experienced cybersecurity marketing firm leverages content depth, structured data, and answer-engine optimization to win zero-click and long-tail moments while feeding ABM programs with context-rich leads.
- Answer real questions succinctly. Build FAQ-style hubs that resolve tactical needs like “how to implement just-in-time access” and “what is SBOM attestation.”
- Use structured data. Mark up definitions, product comparisons, and how-tos so answers surface quickly in rich results.
- Connect content to conversion. Each page should point to hands-on proof such as a lab, PoC, or calculator.
- Instrument relentlessly. Tie rankings to pipeline metrics to keep efforts focused on revenue.
Analytics is the glue. Mature teams bring together keyword universe mapping, competitive gap analysis, and content testing in one operating rhythm. For deeper audience intelligence and testing frameworks, explore Bluetext’s approach to research and analytics and how it informs channel and content decisions that drive measurable impact.
Metrics that matter to the CMO and the board
Security buyers reward rigor, and your measurement model should follow suit. Move beyond traffic and MQL counts to metrics the board values. A cybersecurity marketing firm will benchmark marketing-sourced pipeline, stage-by-stage conversion, velocity, and win-rate differentials for ABM accounts relative to the total addressable market. CAC payback, expansion rates, and multi-product attach are the trailing indicators that prove durable advantage. Align executive dashboards to these measures and ensure quarterly business reviews connect activities to revenue outcomes.
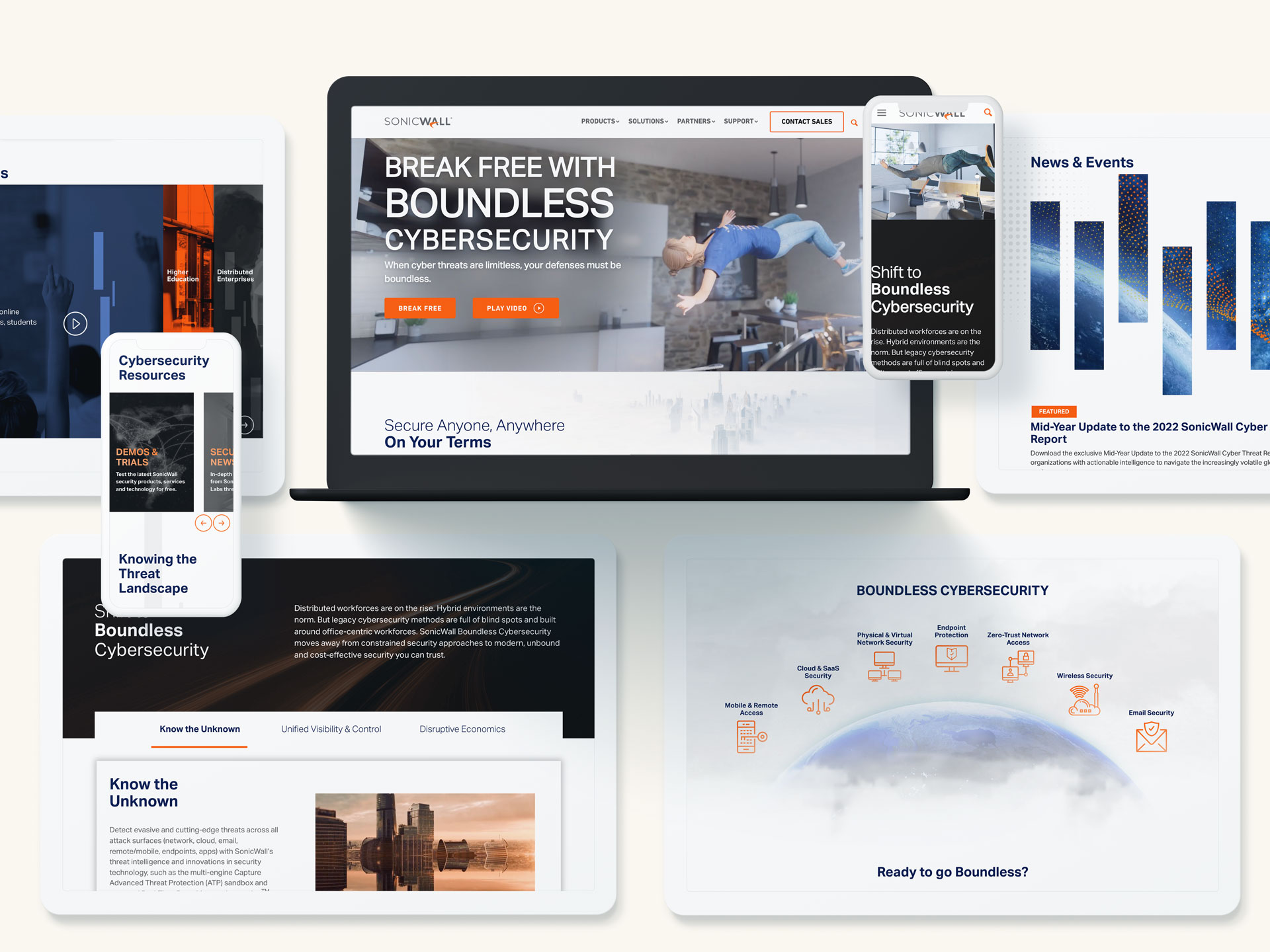
Dig into how we partnered with SonicWall
Selecting the right partner is a force multiplier. Look for a cybersecurity marketing firm that can work across both B2B and B2G motions with credibility. Evaluate their ability to simplify complex architectures without softening the technical truth. Review how they translate emerging trends like identity-first security, CNAPP, and software supply chain integrity into narratives that resonate with both analysts and end users. Ask to see measurement frameworks that tie positioning, content, media, and sales enablement together.
- Category experience. Your partner should have a portfolio that spans endpoint, cloud, identity, data, and OT security so they can anticipate objections and recommend accelerators.
- Brand-to-demand integration. A cybersecurity marketing firm must be equally fluent in brand strategy and demand generation, not one or the other.
- Speed and discipline. Cyber markets move quickly. You need agile sprints and editorial rigor to keep messages current and accurate.
- Public sector fluency. For sellers into government or contractors, ensure the team understands procurement sensitivities and accreditation pathways.
Finally, assess cultural fit. The ideal cybersecurity marketing firm will challenge assumptions, bring fresh creative energy, and embed with your sales and product leaders. They should complement your internal strengths and add the signal you do not have in-house, whether that is research depth, creative scale, or channel specialization.
Accelerating execution with an agency that knows the terrain
Turning strategy into market impact takes cross-functional alignment and polished execution. A specialized cybersecurity marketing agency brings planners, creatives, technologists, and media strategists to the same table so programs launch with momentum and sustain over time. Expect a planning cadence that translates category narrative into quarterly campaign themes, content roadmaps, and field plays. Insist on a creative process that makes complex ideas intuitive for buyers without sacrificing accuracy for speed.
When you evaluate creative, judge it on clarity, memorability, and technical integrity. Ask how the team will tailor core concepts to each route to market, from direct enterprise to channel and OEM relationships. A high-caliber cybersecurity marketing firm will build for modularity so assets repurpose across web, demand gen, events, and sales motions without creating inconsistency or rework.
From brand to proof: where Bluetext adds leverage
Bluetext has partnered with cybersecurity innovators across growth stages to build brands, launch categories, and drive measurable pipeline impact. Our teams synchronize research, positioning, visual identity, content strategy, and activation to deliver a coherent market presence. Explore examples of our work in cybersecurity to see how brand storytelling and technical depth come together in practice. When a cybersecurity marketing firm aligns narrative, creative, and channels, prospects understand your value faster and with more conviction.
We also prioritize the operational realities of enterprise and public sector buyers. From enablement kits that arm sales with objection handling to campaign architectures built for multi-quarter pursuits, the right cybersecurity marketing firm creates systems that scale. That includes structured governance for content accuracy, cross-functional review processes, and analytics models that attribute revenue appropriately across long cycles and complex deals.
A practical 90-day plan to elevate your program
To build momentum quickly, establish a 90-day sprint with clear outcomes and owners. A skilled cybersecurity marketing firm will help you focus on the moves that compound.
- Clarify the promise. Pressure test your one-sentence value proposition with customers and sales. Lock messaging, proof points, and a three-pillar framework.
- Fix the conversion path. Align top-performing pages, demos, and sales handoffs to a single storyline. Reduce friction to the two actions that best predict revenue.
- Publish proof. Release two quantified case studies and one technical validation asset. Promote across search, email, and community channels.
- Stand up intent harvesting. Launch a focused paid search program around your most defensible solution plays. Instrument from click to close.
- Enable the field. Deliver a concise enablement pack with talk tracks, ROI framing, and competitive traps. Train champions to retell the story faithfully.
Within this window, your teams should see higher demo acceptance rates, improved pipeline quality, and faster consensus among buying committees. These are the signals that your narrative, creative, and channel choices are resonating. A data-driven cybersecurity marketing firm will turn those early wins into an operating model that sustains results through the fiscal year.
Ready to elevate your cybersecurity narrative and pipeline
The stakes in security are too high for guesswork. Progress comes from message clarity, credible proof, and disciplined execution. If you are ready to sharpen positioning, strengthen creative, and launch programs that convert complex value into measurable growth, Bluetext can help. Begin the conversation today and see how an experienced cybersecurity marketing firm can turn ambition into market impact. To get started, review our approach, explore relevant case studies, and contact Bluetext to build a plan tailored to your objectives and timelines.
Cybersecurity brands face a paradox. The audience is sophisticated and risk averse, the attack surface changes daily, and buyer committees want proof without exposure. This is why search is both the most important and the most unforgiving channel in the category. SEO for Cybersecurity must translate complex capabilities into trusted, discoverable answers at the exact moment of need. Executives who invest in the right strategy see compounding returns in pipeline quality, analyst visibility, and share of voice. Those who do not watch competitors own high-intent queries, frame market categories, and shape RFP criteria. This article breaks down how to navigate the unique challenges of optimizing for cyber buyers across commercial and public sector landscapes, and how to turn search into an engine for sustainable growth.
Why cybersecurity search dynamics require a different playbook
At first glance, search fundamentals look consistent across industries. In practice, SEO for Cybersecurity behaves differently because queries age quickly, acronyms proliferate, and decision makers prefer proven frameworks over hype. Seasonality is driven by breach news, compliance deadlines, and conference schedules. Content that wins today can slide in weeks if it does not evolve with tactics, TTPs, and regulatory changes. Your program needs a system for continuous refresh and a taxonomy that aligns emerging threats with stable solution concepts.
Fast-moving threats and ephemeral queries
Exploit names and CVE numbers generate short bursts of search volume. Chasing them rarely builds defensible traffic. The better path for SEO for Cybersecurity is to map each news spike to enduring use cases and zero trust, identity, data, or cloud security pillars. Produce rapid-response explainers that redirect interest to evergreen architectures and buyer outcomes. Capture the moment, then hand off to content that compounds.
High-stakes buyers and trust signals
CISOs, security architects, and federal program managers evaluate credibility before they read. Trust begins in the SERP. For SEO for Cybersecurity, prioritize precise titles, clear meta descriptions, and sitelink structure that projects maturity. On the page, showcase certifications, attestations, customer evidence, and third-party validation. Make legal, compliance, and security documentation easy to find. Treat E-E-A-T as table stakes, not a differentiator.
What should your keyword strategy prioritize?
Many teams start with product keywords, then wonder why traffic does not convert. A better framework orders targets by intent and risk posture. Build a core of stable solution, architecture, and framework keywords. Layer problem and detection queries that reflect attacker behavior. Add compliance and public sector terminology that aligns with procurement language. Reserve product and feature queries for conversion hubs. SEO for Cybersecurity gains leverage when it connects these layers through consistent internal linking and clear navigation.
- Solution layer: zero trust network access, identity threat detection, data security posture management.
- Problem layer: lateral movement, privilege escalation, ransomware dwell time.
- Compliance layer: FedRAMP, CMMC, SOC 2, industry-specific mandates.
- Conversion layer: pricing, demos, integrations, supported platforms.
Use query clustering to group related intents. Then assign content types to each cluster. Guides and frameworks for solution queries, deep dives for problems, comparison pages for competitive evaluations, and implementation pages for conversions. This is where SEO for Cybersecurity aligns with buyer enablement rather than just rankings.
How do you build topical authority without oversharing?
Security teams worry that detailed content may help adversaries. The answer is to publish guidance that informs defenders without operationalizing attacks. Focus on methodologies, detection logic concepts, kill chain mappings, and outcome-centric architecture patterns. Create a threat research cadence that deconstructs incidents and maps them to your controls. For SEO for Cybersecurity, this approach delivers depth, not sensitive configuration details. Pair each technical piece with executive summaries that translate risk into business impact and governance.
Editorial governance matters. Establish redlines for sensitive material, review flows with product security and legal, and a process to update posts as the situation changes. This protects brand integrity while compounding authority around your chosen pillars.
How can you win federal and regulated sector searches?
Public sector buyers search differently. They use acquisition terms, contract vehicles, and compliance phrases. To capture this intent, align taxonomy and content to federal frameworks, mission outcomes, and procurement language. Build specific landing pages for FedRAMP status, Authority to Operate pathways, IL levels, and agency use cases. SEO for Cybersecurity should also address state and local standards, critical infrastructure designations, and sector-specific directives. Pair these with case narratives and measurable outcomes appropriate for clearance and disclosure policies.
If federal is a priority, align your plan with proven public sector digital marketing techniques. Integrate FAQs that answer common acquisition questions, publish documentation indexes for contracting officers, and make accessibility compliance explicit. This meets both human and machine expectations for clarity.
What on-page fundamentals matter most right now?
Search engines reward pages that answer questions completely, load quickly, and demonstrate clarity. For SEO for Cybersecurity, emphasize scannability and precision. Use concise H1s and H2s that mirror query language. Open with a plain-language definition and a verdict, then move to architectural context, selection criteria, and next steps. Include schema where relevant, especially FAQPage, Product, Organization, and HowTo for procedural content. Maintain a living glossary for acronyms and standards. Ensure documentation, uptime, and trust center links are one click away for validation.
Performance is non-negotiable. Buyers will not tolerate heavy animations or scripts that slow key pages. Optimize Core Web Vitals without sacrificing brand. Security audiences appreciate speed, clarity, and control more than motion design. That principle alone can lift conversion rates from organic.
How do you earn high-authority links in a risk-averse ecosystem?
Security publications and analysts prefer data-rich, methodology-driven references. Invest in original research, benchmark reports, and tooling that the community finds useful. Host calculative models for risk quantification, maturity assessments, or cost of breach estimates. For SEO for Cybersecurity, this type of asset attracts citations from media, academia, and government. Pair it with a disciplined digital PR program that respects disclosure norms and coordinates with incident response timelines.
If you need the right mix of content, PR, and search orchestration, partner with a specialized cybersecurity marketing agency. Integrated planning ensures your research earns credible coverage and that coverage consolidates authority to the pages that drive pipeline.
Where does content gating help or hurt SEO for Cybersecurity?
Gated content captures known demand. Ungated content builds new demand and authority. The right balance depends on objective and audience. As a rule, ungate executive primers, architectural frameworks, product comparison pages, and implementation guides. Gate analyst-caliber reports, proprietary benchmarks, and calculators that require data inputs, but always provide an ungated summary page with key findings. SEO for Cybersecurity benefits when the summary ranks and the gated asset converts.
Be transparent about data use and privacy. Include a shortform option for government or regulated users who cannot share detailed information. Respect for process reduces form abandonment and builds trust with high-stakes buyers.
How should product and category pages be structured?
Category pages explain problems and solution patterns. Product pages prove fit. For SEO for Cybersecurity, each category page should own a buyer narrative: definition, why it matters now, how to evaluate, selection criteria, and measurable outcomes. Link to deep dives, customer stories, and a comparison to adjacent categories. On product pages, lead with validated use cases, control mappings, integrations, operating environment, and performance at scale. Include a frictionless path to testing, including demo videos, sandbox access, and deployment guides.
Cross-linking between categories and products should be deliberate. Search engines and buyers infer clarity when these relationships are consistent. Avoid orphaned documentation. Bring docs, trust center, and integration directories into the same architecture so SEO for Cybersecurity signals reinforce each other.
How do you align SEO with sales engineering and analyst relations?
Security purchases hinge on validation. Sales engineers, solution architects, and analysts function as trust amplifiers. Build a shared content backlog that captures the most common objections, RFP criteria, and proof points raised in technical evaluations. Then turn these patterns into public answers. For SEO for Cybersecurity, this creates high-intent content that maps directly to how deals advance, not just how pages rank. Coordinate publication calendars with analyst briefings so terminologies match the waves and market guides that shape buyer vocabulary.
Instrument every key page with self-qualifying paths. Offer options to talk to an expert, run a guided assessment, or explore a lab environment. Attach measurement to each outcome so marketing and sales share a single view of contribution to pipeline.
What metrics should executives track beyond traffic?
Pageviews do not earn renewals. Executive dashboards must show how search contributes to revenue, influence, and market leadership. For SEO for Cybersecurity, prioritize:
- Share of voice across target clusters and competitive benchmarks.
- Coverage of critical topics by funnel stage, mapped to win rates.
- Assisted and direct pipeline from organic sessions at the account level.
- Content velocity and refresh rate on priority pages.
- Quality signals such as engagement depth, documentation downloads, and trust center interactions.
Link dashboards to your revenue operations model so attribution, velocity, and conversion logic are credible to finance and the board. Treat rankings as leading indicators, not the goal. The goal of SEO for Cybersecurity is qualified demand at sustainable CAC, with content that compresses due diligence time.
What does a pragmatic 18-month roadmap look like?
An effective plan moves in phases, each with clear exit criteria. Month 0 to 3 focuses on technical foundations, IA redesign, and a prioritized content backlog. Month 4 to 9 builds authoritative category and solution hubs, launches research assets, and scales digital PR. Month 10 to 18 optimizes conversion paths, expands into adjacent topics, and operationalizes refresh cadences. Throughout, maintain a rolling threat-to-solution mapping process so current events continuously connect to evergreen content. SEO for Cybersecurity succeeds when cadence beats chaos.
For a model of integrated planning, review Bluetext’s approach to search engine optimization and how strategy, content, design, and media reinforcement come together. The right orchestration compresses timelines and compounds authority.
How do you resource the program without overextending SMEs?
Subject matter experts are essential but scarce. Protect their time by codifying interview playbooks, creating reusable outlines by topic type, and enabling iterative reviews rather than ground-up rewrites. For SEO for Cybersecurity, pair a senior editor with each pillar to maintain voice and accuracy. Build a content ops rhythm that batches SME reviews and aligns with release trains. This reduces cycle time and preserves technical integrity.
Augment SMEs with research analysts and technical writers who understand ATT&CK, NIST, and cloud shared responsibility models. The combination yields content that is both discoverable and defensible, which is the core advantage in cybersecurity search.
Case-in-point outcomes you can expect
Teams that execute this model typically see faster growth in qualified organic sessions than in raw traffic. Branded search expands as category leadership takes hold. Comparison and evaluation pages become top converters. Earned media citations concentrate on research assets, lifting the authority of entire hubs. For enterprise or public sector pursuits, SEO for Cybersecurity improves influence on multi-threaded deals as procurement teams validate capabilities through ungated content and documentation.
The second-order effect is strategic. When your definitions and selection criteria rank, you shape how buyers frame the problem. That influence ripples into analyst reports, partner narratives, and ultimately, shortlists. This is why leadership treats search as a market-making function, not just a demand capture channel.
Common pitfalls to avoid
Several predictable mistakes slow or stall programs in this sector. Avoid them to keep momentum and credibility intact.
- Chasing news over narrative. Trend posts without a connection to stable solution hubs do not compound authority.
- Gating everything. If buyers cannot verify claims without a form, they will bounce to competitors.
- Bloated pages. Security audiences want fast answers and clear architecture, not dense prose.
- Disconnected docs. Trust center, compliance, and integration content should live in the same navigational system.
- Ignoring B2G language. Public sector searches follow acquisition conventions that require dedicated content.
- Underinvesting in PR. SEO for Cybersecurity needs authoritative links that usually come from research-driven storytelling.
How Bluetext accelerates results for cybersecurity leaders
Bluetext has helped growth-stage and enterprise security brands define categories, clarify architectures, and win high-intent searches that move pipeline. Our integrated teams pair positioning and message architecture with technical content, UX, digital PR, and analytics. We architect programs so executive stakeholders can see contribution to revenue and brand leadership, not just traffic. Explore our work in cybersecurity for examples of narrative clarity, design systems, and campaign orchestration built for complex buyer journeys.
This sector demands a partner that knows how security leaders think and how search engines evaluate expertise. When you are ready to transform how the market discovers, understands, and trusts your solutions, contact Bluetext. If you need a broader integrated approach across brand and campaigns, our cybersecurity marketing capability and public sector digital marketing expertise can support every step of the journey. We will build an SEO for Cybersecurity program that compounds authority, reduces acquisition costs, and creates a durable advantage in the moments that matter.
Prefer listening over reading? Check out the podcast version of this blog below and enjoy insights on the go!
Security teams cannot defend what they cannot see, and the same truth applies to marketing. If your solutions, guidance, or research are invisible in search, the buyers who need you most will never find you. SEO for Cybersecurity aligns your brand, content, and technical infrastructure with the way CISOs, SOC leaders, procurement officers, and researchers actually search during critical moments. Done well, it increases qualified demand, compresses sales cycles, and strengthens digital trust at the precise moments that shape the outcome of a deal or crisis. For modern marketing leaders, SEO is not a channel to check off a list. It is a strategic capability that directly supports pipeline resilience and brand credibility in a volatile threat landscape.
What is SEO, and why does it matter now?
SEO focuses on the unique needs, search behaviors, and risk thresholds of security decision-makers. It elevates content that answers high-stakes questions across prevention, detection, and response. When a ransomware incident hits and a buyer searches for immediate help, the cybersecurity providers who have invested in SEO will appear with credible guidance and clear actions. That visibility translates to trust, and trust becomes a new business conversation. In B2G, where procurement rigor and compliance considerations are extensive, the right search visibility shortens discovery and validates a vendor’s authority early.
The cybersecurity market has matured beyond vanity keywords. Today, SEO prioritizes the intersection of intent, expertise, and speed. Executive buyers search differently from practitioners. Federal audiences search differently from enterprise teams. Search results pages have also shifted to favor authoritative answers and structured information, not just blogs with superficial coverage. The companies winning organic share are those that bring deep expertise to their content, reinforce it with technical excellence, and maintain rapid publishing cadences for emerging threats.
How should cybersecurity brands structure an intent-led content strategy?
The foundation of SEO is a content model built around buyer intent. Map topics to real scenarios and decision stages. Example categories include executive explainers on zero trust architecture, practitioner deep dives on SIEM tuning or EDR comparisons, and emergency guides for incident response. Every topic should have a clear purpose, a defined target persona, and an obvious next step.
- Define evergreen pillars: security operations maturity, vulnerability management, identity security, cloud posture, and compliance frameworks. Use these as permanent hubs for your authority.
- Create fast-turn clusters: pages for new CVEs, ransomware variants, and supply chain vulnerabilities. The brands that operationalize rapid publishing are the brands buyers bookmark.
- Build B2G tracks: content tailored to procurement workflows, ATO timelines, FedRAMP considerations, and interagency collaboration. These tracks support SEO for Cybersecurity while acknowledging public sector constraints.
Format matters. Technical evaluators favor detailed comparisons, architecture diagrams, and deployment runbooks. Executives want concise risk framing, total cost narratives, and case studies that show time to value. Both groups respond to content that is skimmable, accurate, and transparent. Successful SEO balances depth with clarity and uses structured elements such as checklists and step-by-step playbooks to satisfy search intent quickly.
What technical SEO improvements make the biggest impact for cyber brands?
Security audiences have low patience for slow or unreliable websites. Core Web Vitals, clean architecture, and robust internationalization are table stakes. Start with a streamlined site taxonomy that reflects how buyers navigate from high-level strategy to solution detail. Use internal linking to guide movement between related topics and to surface high-intent pages. Strong information architecture makes SEO in the cybersecurity industry more resilient as you scale content across products and markets.
Implement structured data wherever it informs the searcher. Product, FAQ, How To, and Article schema can improve discoverability and sitelink coverage. For vulnerability advisories and CVE documentation, standardized labeling and precise metadata are essential. Accelerate indexing with clear sitemaps and a publishing process optimized for speed and version control. If you run status or incident hubs, apply thoughtful indexation rules so that public communications are discoverable while sensitive operational pages remain controlled.
Security buyers often prefer browsing on locked-down devices or via mobile during off-hours. Mobile responsiveness, reliable HTTPS configuration, and lightweight code become competitive advantages. Combine technical cleanliness with measured pacing of scripts and trackers. That improves user experience and reduces the likelihood of false positives with endpoint protections. The end result is a technical foundation that supports SEO without introducing friction.
How do credibility, E-E-A-T, and digital PR reinforce search authority?
Cybersecurity is a YMYL category where expertise and trust are non-negotiable. Elevate named authors with verifiable credentials. Publish real research with original data, not recycled commentary. Provide transparent editorial standards and update logs on time-sensitive content. When you demonstrate experience and authority, search engines and buyers reward you. This is the essence of SEO in high-stakes categories.
Your backlink strategy should mirror the industry’s trust graph. Prioritize mentions and citations from respected analyst outlets, academic communities, standards bodies, and industry associations. Avoid low-quality link schemes that risk reputational damage. Run digital PR around responsible vulnerability disclosures, joint research with partners, and policy commentary that adds genuine value. As these signals accumulate, they compound the impact of SEO and protect your brand during crises.
What role does thought leadership play in demand generation?
Effective thought leadership turns organic demand into pipeline. Long-form guides on NIST CSF alignment, zero trust implementation roadmaps, and MDR vs. XDR decision frameworks meet buyers where they are. Pair these assets with calculators that quantify risk reduction or SOC efficiency gains. Package learnings into short executive briefs for the C-suite and deeper technical documentation for practitioners. When thought leadership drives clarity, it accelerates qualified conversations and strengthens SEO across priority topics.
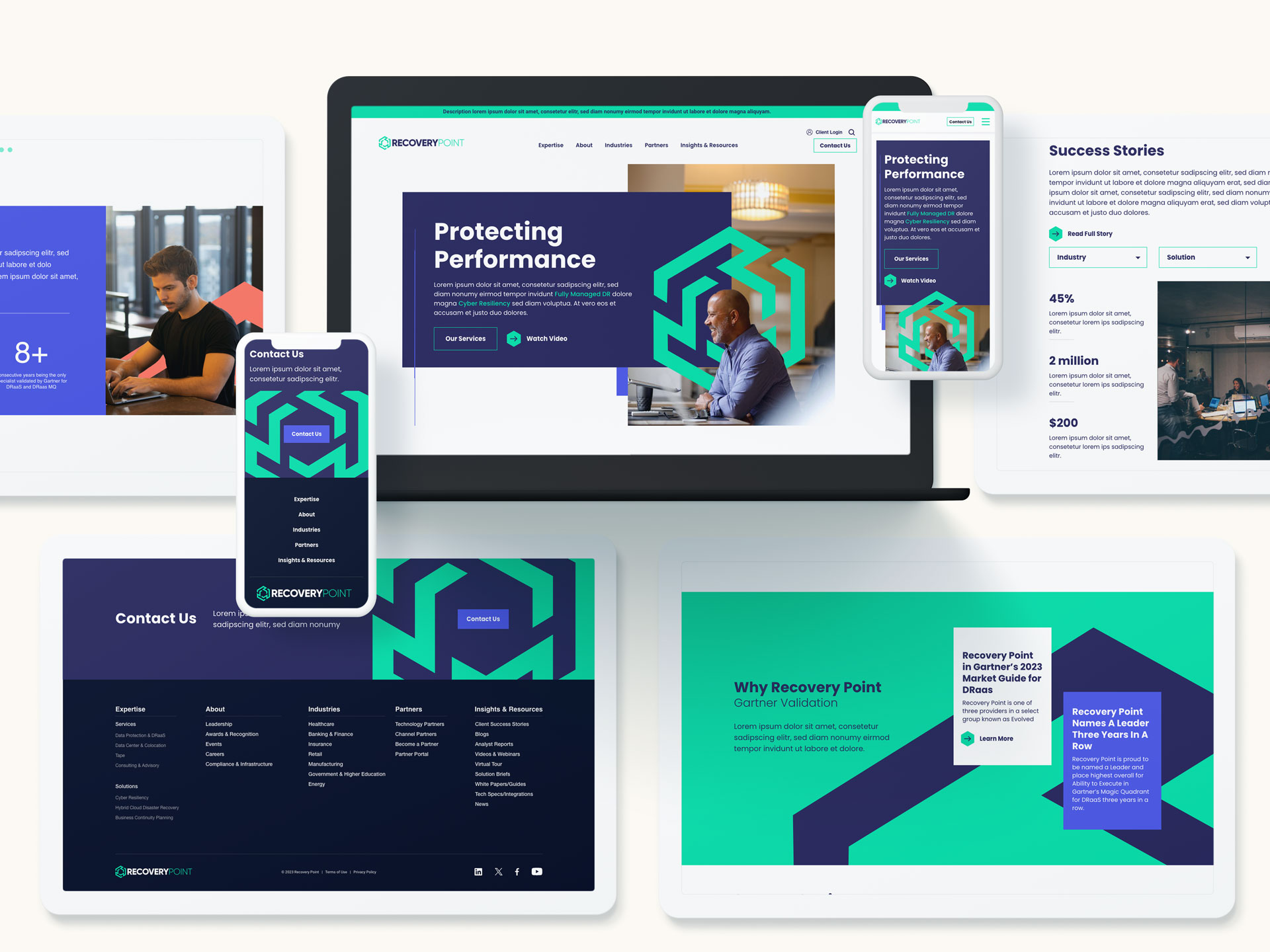
How do B2G requirements change the SEO approach?
Public sector buyers face distinct procurement steps, compliance gates, and budget rhythms. Content must speak to these realities: authority to operate, cloud security posture, supply chain integrity, and vendor risk management. Create pages that align with key contract vehicles, timelines, and compliance milestones. Above all, use precise language and avoid marketing abstractions. Clear alignment to mission outcomes increases trust and drives performance in SEO for federal and state audiences.
Localization often helps. When targeting specific agencies or regions, reflect their terminology, use cases, and regulatory references. Build structured pages that address common questions from contracting officers and technical evaluators. Offer credible proof points: implementation timelines, integration patterns with government tech stacks, and support models. This directly supports SEO by reducing ambiguity and highlighting measurable value.
How can SEO mitigate crisis risk and support incident response?
During a security event, search becomes a truth-seeking channel. Plan for “brand + breach” and “brand + vulnerability” scenarios with prebuilt playbooks. Create a response hub that centralizes verified updates, FAQs, and remediation steps. Use canonical signals to avoid outdated information outranking current guidance. Coordinate PR, legal, security, and marketing teams to publish quickly and coherently. Placing accurate, helpful content in the SERP is a tangible way SEO defends reputation when it matters most.
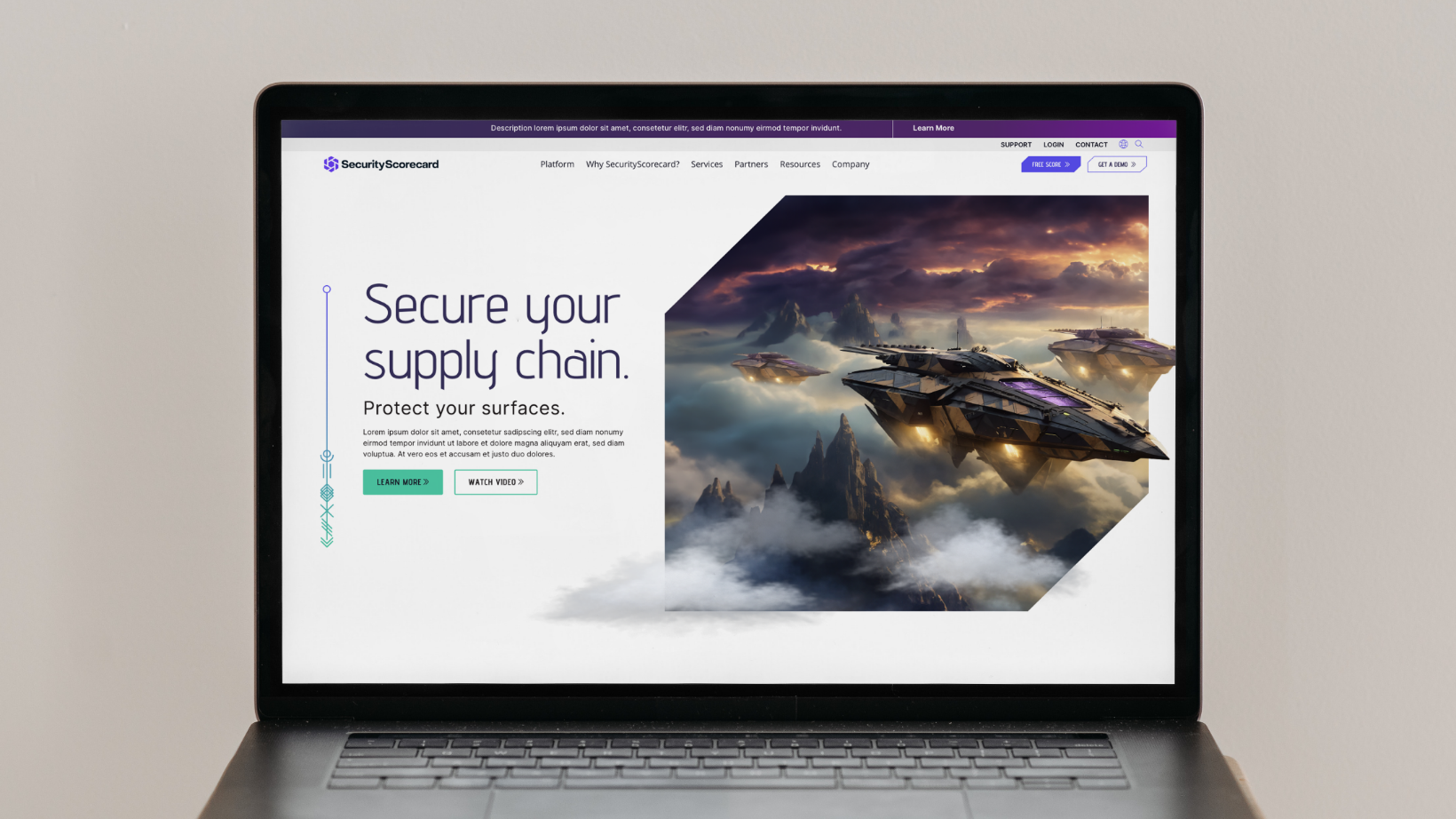
What metrics prove value to the C-suite?
Executives need proof that organic performance drives business outcomes. Move beyond traffic and rank positions. Track assisted revenue, pipeline influence, share of search in target categories, and conversion quality by intent. Measure how often buyers who entered via organic convert to sales-qualified opportunities compared to paid channels. These indicators make the ROI case for SEO for Cybersecurity with clarity and credibility.
Layer in operational diagnostics: indexing efficiency, time to publish for critical content, and visibility for executive queries like “best zero trust vendors” or “incident response retainer.” Monitor brand SERP health, including sitelinks, knowledge panels, and presence of third-party reviews. Analyze log files to identify crawl waste and prioritize technical fixes. This discipline ensures SEO remains a durable growth engine rather than a reactive project.
How do you operationalize SEO for complex security portfolios?
Organize teams around topics, not just products. Establish a governance model with editorial standards, SME review cycles, and an always-on calendar for emerging threats. Build cross-functional rituals among product marketing, research, comms, and demand gen. Equip the team with templates for comparison pages, advisory posts, implementation guides, and FAQs. Systematizing production improves speed and consistency, which directly strengthens SEO at scale.
Finally, connect organic insights to broader go-to-market motions. Feed search intent data into ABM lists, paid search negatives, webinar themes, and sales enablement. Use organic performance to inform product naming, messaging pillars, and positioning tests. When SEO is integrated with brand, creative, and campaigns, the entire program becomes greater than the sum of its parts.
Move from visibility to velocity with Bluetext
Security markets reward clarity, speed, and credibility. That is exactly what a modern, integrated program delivers when SEO is built into your brand, content, and digital infrastructure. If you are ready to capture high-intent demand, strengthen your authority with decision-makers, and operationalize fast, reliable publishing, Bluetext can help. Contact our team to elevate your strategy, sharpen your positioning, and launch campaigns that turn search into sustained growth.
Prefer listening over reading? Check out the podcast version of this blog below and enjoy insights on the go!
Cybersecurity companies operate in one of the most competitive and complex markets in B2B. The stakes are high, the technology is sophisticated, and buyers are increasingly skeptical. While demand for cybersecurity solutions continues to grow, many companies struggle to communicate their value clearly and consistently.
Marketing in this space is fundamentally different from other B2B categories. Success depends on more than lead generation or brand awareness. It requires clarity, credibility, and a deep understanding of how security buyers evaluate risk. For many organizations, working with a specialized cybersecurity marketing agency becomes essential to navigating these challenges effectively.
Why Cybersecurity Marketing Is Uniquely Challenging
Cybersecurity marketing sits at the intersection of technical complexity and business risk. Products are often highly specialized, yet buyers range from deeply technical practitioners to executive decision-makers focused on financial and operational impact.
Adding to the challenge, the market is crowded. New vendors emerge constantly, many using similar language and claims. Buyers are inundated with messaging that promises protection, visibility, or resilience, making it difficult for any single brand to stand out.
Trust also plays an outsized role. In cybersecurity, credibility is not optional. Prospective customers must believe that a vendor understands the threat landscape and can protect critical systems. Marketing that feels exaggerated, vague, or overly promotional can quickly undermine confidence.
Challenge 1: Translating Technical Complexity Into Clear Value
One of the most common pitfalls in cybersecurity marketing is an overemphasis on features and technical capabilities. While accuracy matters, deeply technical messaging often fails to resonate with buyers who are focused on outcomes rather than architecture.
Security leaders care about reducing risk, improving response times, and maintaining compliance. Executives want to understand how a solution protects the business, minimizes disruption, and supports long-term resilience. When messaging does not connect technology to these priorities, it creates friction in the buying process.
This challenge is especially pronounced for early-stage and mid-market cybersecurity companies, where product innovation can outpace marketing maturity.
Overcoming Complexity With Strategic Messaging
Effective cybersecurity marketing starts with a disciplined messaging strategy. This means identifying the core problems the product solves and articulating them in language that resonates with different audiences.
A strong messaging framework speaks to both technical and business stakeholders without oversimplifying or diluting accuracy. It prioritizes clarity, relevance, and consistency across channels. Use cases, real-world scenarios, and proof points help ground abstract capabilities in tangible outcomes.
A cybersecurity marketing agency brings structure to this process. With category experience, they know how to balance precision with accessibility, ensuring that complex offerings are understood and remembered.
Challenge 2: Building Trust in a High-Stakes Market
Trust is the foundation of every cybersecurity purchase. Buyers are evaluating vendors not just on functionality, but on reliability, expertise, and long-term viability. Any perception of risk or uncertainty can derail a deal.
For newer companies, establishing credibility is often the biggest hurdle. For established firms, maintaining trust while evolving the brand or expanding into new markets can be equally challenging.
Marketing missteps, such as overpromising results or relying on buzzwords, can quickly erode confidence. In cybersecurity, buyers expect accuracy, transparency, and depth.
Strategies for Establishing Credibility and Authority
Building trust requires consistency over time. Thought leadership plays a critical role, particularly when it demonstrates genuine understanding of the threat landscape and emerging challenges. Content should educate rather than sell, positioning the company as a knowledgeable and reliable partner.
Brand consistency is equally important. From visual identity to tone of voice, every touchpoint should reinforce professionalism and credibility. Customer proof, analyst recognition, and third-party validation help further reduce perceived risk.
A marketing agency for cybersecurity companies understands how to build authority without exaggeration. They focus on long-term brand equity alongside near-term campaign performance.
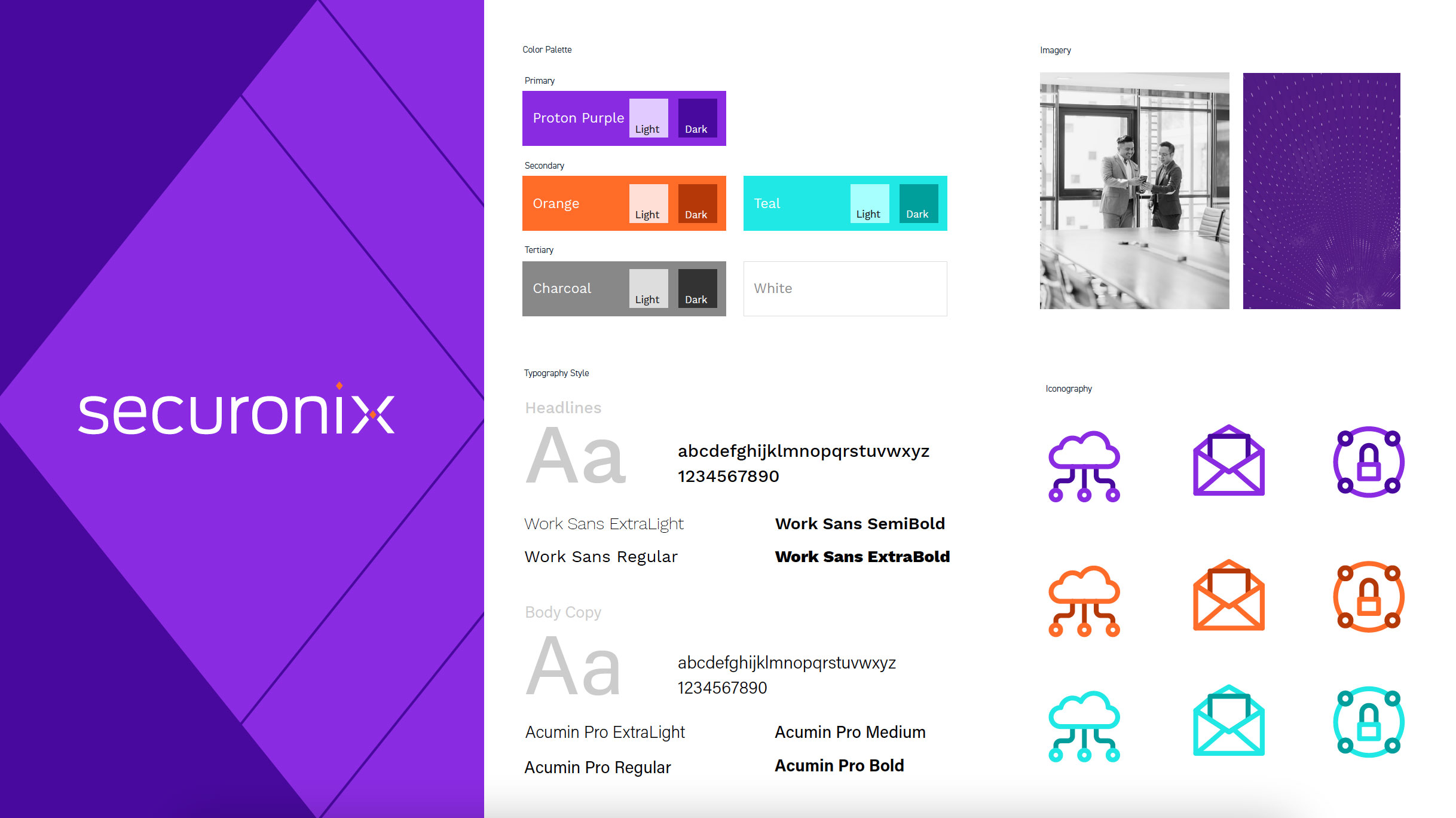
Challenge 3: Differentiating in a Saturated Cybersecurity Landscape
Differentiation is one of the most persistent challenges in cybersecurity marketing. Many vendors offer overlapping capabilities, and industry language has become increasingly homogenized.
Claims around visibility, protection, and intelligence are common, making it difficult for buyers to discern meaningful differences. Feature-based differentiation often collapses under scrutiny, especially when competitors make similar claims.
Without clear positioning, marketing efforts risk blending into the background, regardless of product quality.
Creating Differentiation Through Brand Strategy
True differentiation comes from strategic positioning, not feature lists. Effective cybersecurity brands define who they serve, what problems they solve best, and why their approach is distinct.
This requires making deliberate choices. Not every buyer is the right buyer, and not every capability needs equal emphasis. Clear positioning helps focus messaging, guide campaign development, and align sales and marketing teams.
A cybersecurity marketing agency brings an external perspective that helps uncover defensible points of differentiation. By aligning brand strategy with business objectives, companies can cut through noise and communicate value more effectively.

Challenge 4: Reaching Multiple Buyers With Conflicting Priorities
Cybersecurity buying decisions rarely rest with a single individual. Security practitioners, IT leaders, CISOs, and executives all influence the process, often with different priorities and concerns.
Marketing must address technical depth without alienating non-technical stakeholders. Content that resonates with security teams may not land with executive buyers, and vice versa. This complexity makes one-size-fits-all messaging ineffective.
Understanding where and how each audience engages is critical to building effective campaigns.
Campaign Strategies That Drive Engagement and Results
Successful cybersecurity campaigns are integrated and intentional. Brand, content, digital, and demand efforts should work together to support long sales cycles and complex decision-making processes.
Measurement frameworks must reflect these realities. While leads and conversions matter, engagement quality and pipeline influence often provide more meaningful insight. Metrics such as account engagement, content performance, and sales alignment help connect marketing activity to revenue outcomes.
A marketing agency for cybersecurity companies brings experience designing campaigns that balance brand building with performance, ensuring that marketing supports growth at every stage.
Why Specialized Cybersecurity Marketing Expertise Matters
Generalist B2B marketing approaches often fall short in cybersecurity. Without category knowledge, agencies can struggle with messaging accuracy, credibility, and buyer expectations.
A specialized cybersecurity marketing agency understands the nuances of the space, from regulatory considerations to evolving threat narratives. This expertise accelerates strategy development and reduces the risk of missteps that can damage trust.
For many cybersecurity companies, partnering with an experienced agency allows internal teams to focus on product innovation while ensuring marketing execution remains disciplined and effective.
Turning Marketing Challenges Into Competitive Advantage
Cybersecurity marketing challenges are significant, but they are not insurmountable. Companies that invest in clarity, credibility, and strategic alignment are better positioned to stand out in crowded markets.
By addressing complexity through strong messaging, building trust through consistent brand execution, and differentiating through clear positioning, cybersecurity companies can transform marketing into a growth driver.
The right agency partnership can make the difference between blending in and leading the conversation. With the right strategy and execution, marketing becomes a competitive advantage rather than a bottleneck.
Ready to turn complex cybersecurity offerings into clear, compelling marketing?
Bluetext partners with cybersecurity companies to clarify positioning, build trust, and create marketing strategies that support real business growth. If you’re looking for a team that understands the cybersecurity landscape and knows how to translate technical depth into impact, let’s talk.
Not all marketing strategies work equally well for cybersecurity firms. Unlike traditional B2B businesses, cyber companies face unique challenges—complex solutions, highly technical audiences, and the critical need to establish trust with decision-makers. That’s why partnering with a cyber security marketing agency can make all the difference. From content marketing to LinkedIn campaigns, a specialized agency can help your brand reach the right audience while driving measurable results.
In this article, we’ll explore five proven marketing strategies that cybersecurity companies can leverage to grow their brand, generate leads, and position themselves as thought leaders in the space.
1. Thought Leadership Content Marketing
Content marketing remains one of the most effective ways for cybersecurity companies to build credibility. With high-value resources like white papers, case studies, technical blogs, and industry reports, your company can educate prospects and demonstrate expertise.
A cyber security marketing agency knows how to tailor content for technical audiences without overwhelming them. The right approach balances in-depth analysis with readability, helping your firm become a trusted advisor. By sharing actionable insights and highlighting success stories, your company can engage prospects early in the buying journey.
Tips for implementation:
- Develop educational white papers or research reports addressing industry pain points.
- Regularly publish technical blogs and LinkedIn articles for maximum reach.
- Include CTAs in content to capture leads, such as gated resources or newsletter sign-ups.
When done correctly, content marketing builds trust, positions your brand as an authority, and drives qualified leads to your sales team.
2. LinkedIn and B2B Social Media Campaigns
LinkedIn is the go-to platform for B2B cybersecurity marketing. Decision-makers, executives, and IT leaders spend time here, making it ideal for connecting with your target audience.
A cyber security marketing agency can create highly targeted campaigns that speak directly to your ideal clients. From sponsored content and carousel ads to employee advocacy programs, LinkedIn campaigns amplify reach while maintaining professional credibility.
Key strategies:
- Target posts to decision-makers at companies most likely to benefit from your solutions.
- Use video snippets or carousel ads to showcase product capabilities or client success stories.
- Encourage employees to share branded content to extend organic reach.
Metrics such as engagement rate, lead generation, and conversion tracking help you measure the impact of your campaigns and optimize for better performance over time.

3. Account-Based Marketing (ABM) for High-Value Targets
For cybersecurity companies, not all leads are created equal. Some organizations represent significantly higher revenue potential than others. Account-Based Marketing (ABM) allows you to focus your efforts on high-value targets through personalized campaigns.
An experienced cyber security marketing agency can implement ABM strategies, tailoring messaging, content, and outreach to each account. This approach strengthens relationships, increases engagement, and improves conversion rates, especially for complex solutions that require multiple decision-makers.
ABM tactics to consider:
- Personalized email sequences and content tailored to specific accounts.
- Custom landing pages for target companies.
- Executive webinars or VIP events to showcase expertise and solutions.
By investing in ABM, your company prioritizes quality over quantity, ensuring marketing resources are spent where they will yield the highest return.
4. Search Engine Optimization (SEO) for Cybersecurity Firms
Even in a niche industry like cybersecurity, prospects start their journey with online research. Appearing in search results for relevant queries is critical for generating inbound leads.
SEO for cybersecurity companies requires a strategic approach that combines technical optimization, keyword targeting, and content creation. A cyber security marketing agency can help identify high-value search terms and optimize content to increase visibility and drive organic traffic.
SEO best practices for cybersecurity marketing:
- Use industry-specific keywords, such as “cybersecurity solutions” or “threat intelligence software.”
- Optimize website architecture and page load speeds for user experience.
- Publish authoritative content that addresses customer pain points and questions.
By maintaining a consistent SEO strategy, your company ensures prospects find you when researching solutions, reducing reliance on costly paid campaigns and establishing long-term organic visibility.
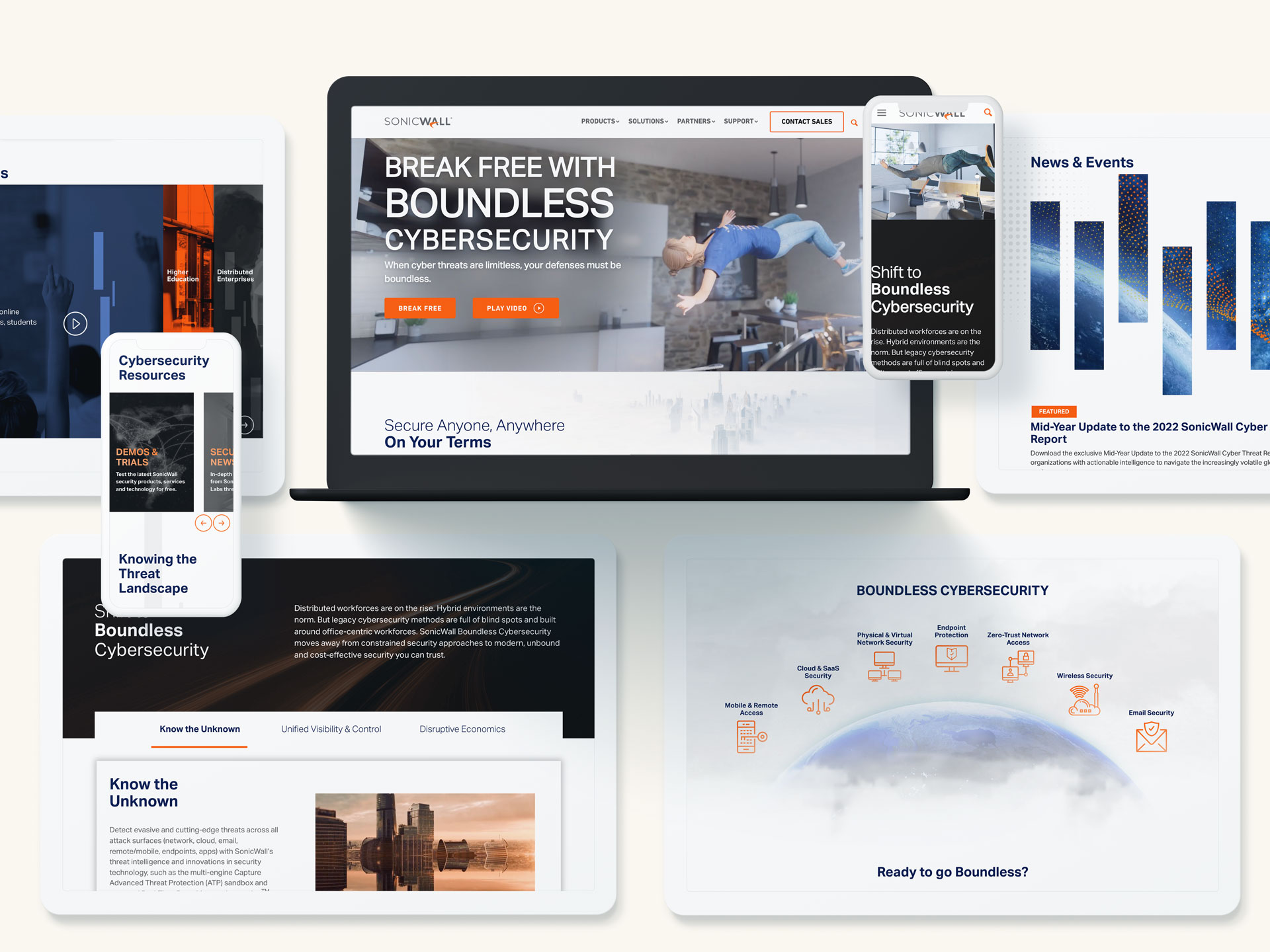
5. Strategic Partnerships and Industry Events
Networking and partnerships are often overlooked but highly effective for cybersecurity marketing. Events, conferences, and webinars allow you to connect with potential clients while demonstrating expertise.
A cyber security marketing agency can manage event marketing, sponsorships, and co-marketing opportunities, ensuring your brand receives maximum visibility. Partnerships with complementary vendors also expand your reach and credibility within the industry.
Ways to leverage partnerships and events:
- Host webinars or panel discussions featuring industry experts.
- Sponsor or participate in cybersecurity conferences.
- Collaborate with vendors or industry associations for co-branded campaigns.
Events and partnerships not only generate leads but also strengthen brand awareness and reinforce your company’s position as a trusted authority in cybersecurity.
Transform Your Cybersecurity Marketing with Expertise
Marketing a cybersecurity company requires a strategic and specialized approach. By leveraging thought leadership content, LinkedIn campaigns, ABM, SEO, and industry partnerships, your brand can generate qualified leads, build credibility, and differentiate itself from competitors.
Partnering with a cyber security marketing agency ensures these strategies are implemented effectively, with measurable results that drive business growth. Whether you’re looking to improve content, increase lead generation, or expand your industry presence, a specialized agency brings the expertise and experience your cybersecurity firm needs to succeed.
Ready to elevate your cybersecurity marketing? Contact Bluetext today to start building a strategy that drives results.
Marketing a cybersecurity company is fundamentally different from marketing any other category in technology. Buyers operate in an environment defined by high-stakes decisions, rapid threat evolution, and intense scrutiny over vendor credibility. As a result, cybersecurity firms must communicate with clarity, precision, and authority if they want to stand out. Working with a specialized Cyber Security Marketing Agency gives organizations the strategic advantage they need to differentiate themselves, generate qualified leads, and build trust in a market where trust is everything.
The High-Stakes Reality of Cybersecurity Marketing
Cybersecurity buying cycles are shaped by urgency, complexity, and risk. CISOs, CIOs, SecOps teams, and procurement leaders are expected to make defensible decisions on vendors who can safeguard critical data, infrastructure, and operations. Trust is not a “nice-to-have”—it is the foundation of every interaction.
In a landscape with hundreds of point solutions, overlapping capabilities, and constant new entrants, cybersecurity companies cannot rely on generic marketing programs to break through. Messaging must be both technically sound and business-focused, and digital experiences must signal credibility from the moment a prospect discovers your brand. A specialized Cyber Security Marketing Agency understands this context and builds strategies tailored to it.
Why Cybersecurity Marketing Requires a Different Approach
Cybersecurity firms face several challenges that set them apart from other B2B technology companies:
- Deep Skepticism Among Buyers
Technical buyers evaluate not only what you claim but whether you can prove it. They expect detailed explanations, real architectures, and third-party validation before they engage. - Complex, Highly Technical Solutions
Cybersecurity products often involve advanced capabilities—from threat intelligence and zero trust architectures to MDR, XDR, IAM, and cloud security. Translating this complexity into accessible, business-aligned messaging requires specialized experience. - Compliance and Regulatory Pressure
FedRAMP, CMMC, SOC 2, ISO, GDPR, and industry-specific mandates influence buying decisions. Marketing must accurately reflect compliance maturity without overstating or oversimplifying. - Evolving Threat Landscapes
Threat actors move fast, and messaging cannot remain static. Cyber firms need agile content strategies that reflect current trends, emerging risks, and new vulnerabilities.
These challenges demand a marketing partner fluent in the nuances of cybersecurity technology, buyers, and industry dynamics.

What a Specialized Cyber Security Marketing Agency Brings to Your Brand
Partnering with an agency that works exclusively or primarily with cybersecurity and advanced technology brands gives your organization strategic advantages that generalist agencies simply cannot match.
Deep Expertise in Cybersecurity Messaging
Specialized agencies understand the technologies, architectures, and use cases security buyers care about. They can translate technical capabilities into business-ready value propositions without diluting accuracy or depth. This accelerates the creation of messaging frameworks, solution positioning, and product marketing materials.
Insight Into Cybersecurity Buyer Personas
A Cyber Security Marketing Agency knows how CISOs, SOC leaders, architects, analysts, and procurement teams evaluate vendors. This includes how they research solutions, what pain points matter, and what content they expect throughout the buying cycle.
Experience Delivering Integrated Cybersecurity Demand Generation
From top-of-funnel thought leadership to ABM programs targeting enterprise and federal buyers, specialized agencies build demand engines that align with security buying cycles. They leverage cybersecurity-specific intent data, multi-channel campaigns, high-value gated assets, and nurture tracks calibrated for long evaluation windows.
Credibility-Centered Brand and Digital Strategy
Cybersecurity brands must signal trust instantly. A specialized agency brings experience designing websites, visual identities, and digital experiences that reflect security, maturity, and technical authority.

Positioning Your Firm for True Differentiation
In a category where many companies claim “real-time detection,” “AI-powered defense,” or “end-to-end security,” meaningful differentiation is rare. A specialized agency helps identify and articulate the white space your firm can authentically own.
This includes:
- Developing a clear and defensible narrative.
- Distilling technical innovation into buyer-friendly language.
- Building a messaging hierarchy that supports sales conversations and product roadmaps.
- Creating solution architectures that communicate how your platform or services fit into broader security ecosystems.
Differentiation is not about louder messaging—it is about smarter, clearer positioning.
Fueling Growth Through a Modern Cybersecurity Demand Engine
Cybersecurity buyers rely heavily on content to inform shortlists and vendor decisions. A Cyber Security Marketing Agency builds integrated demand programs grounded in the needs of these buyers, including:
- Threat briefings, technical guides, and solution overviews.
- Whitepapers, webinars, and demos tailored for security leaders.
- ABM campaigns aligned to enterprise and federal procurement cycles.
- Multi-touch nurture programs built around personas and intent signals.
This approach ensures every campaign drives meaningful engagement and qualified pipeline, not vanity metrics.
Building a Trusted Digital Presence
Your website and digital content are often the first point of validation for cybersecurity buyers. A specialized agency knows how to build experiences that project maturity, technical credibility, and ease of navigation.
Best practices include:
- Clear articulation of your platform or services.
- Conversion paths that align to cybersecurity buyer behavior.
- High-value content tied to industry trends, emerging threats, and regulatory changes.
- SEO strategies designed for a competitive, rapidly shifting search landscape.
Effective cybersecurity marketing does not rely on trends—it relies on clarity, authority, and consistency.
Elevating Brand Authority Through Thought Leadership
Security leaders look for partners who demonstrate depth, foresight, and expertise. Thought leadership is one of the most effective tools for establishing this authority.
A Cyber Security Marketing Agency supports brands by developing:
- Research-backed threat reports.
- Executive commentary for industry publications.
- Podcast and video content featuring SMEs.
- Analyst engagement strategies that enhance visibility.
- Perspectives on emerging threats, evolving regulations, and best practices.
The result is a brand that feels credible, informed, and indispensable to security conversations.
Why Bluetext Is the Right Partner for Cybersecurity Brands
Bluetext has a long track record of supporting cybersecurity, federal, defense, and advanced technology organizations as they scale and evolve. Our team understands the complexity of cybersecurity products and the sophistication of the audiences evaluating them. We bring deep experience in branding, digital experience design, product marketing, campaigns, and demand generation tailored to the needs of security buyers.
Whether your firm is entering a new market, rethinking its narrative, building a modern website, or launching integrated demand programs, Bluetext helps you put your best foot forward—and stay ahead of competitors who are moving fast.
To learn how Bluetext can support your cybersecurity marketing strategy, contact us today.