Cybersecurity brands face a paradox. The audience is sophisticated and risk averse, the attack surface changes daily, and buyer committees want proof without exposure. This is why search is both the most important and the most unforgiving channel in the category. SEO for Cybersecurity must translate complex capabilities into trusted, discoverable answers at the exact moment of need. Executives who invest in the right strategy see compounding returns in pipeline quality, analyst visibility, and share of voice. Those who do not watch competitors own high-intent queries, frame market categories, and shape RFP criteria. This article breaks down how to navigate the unique challenges of optimizing for cyber buyers across commercial and public sector landscapes, and how to turn search into an engine for sustainable growth.
Why cybersecurity search dynamics require a different playbook
At first glance, search fundamentals look consistent across industries. In practice, SEO for Cybersecurity behaves differently because queries age quickly, acronyms proliferate, and decision makers prefer proven frameworks over hype. Seasonality is driven by breach news, compliance deadlines, and conference schedules. Content that wins today can slide in weeks if it does not evolve with tactics, TTPs, and regulatory changes. Your program needs a system for continuous refresh and a taxonomy that aligns emerging threats with stable solution concepts.
Fast-moving threats and ephemeral queries
Exploit names and CVE numbers generate short bursts of search volume. Chasing them rarely builds defensible traffic. The better path for SEO for Cybersecurity is to map each news spike to enduring use cases and zero trust, identity, data, or cloud security pillars. Produce rapid-response explainers that redirect interest to evergreen architectures and buyer outcomes. Capture the moment, then hand off to content that compounds.
High-stakes buyers and trust signals
CISOs, security architects, and federal program managers evaluate credibility before they read. Trust begins in the SERP. For SEO for Cybersecurity, prioritize precise titles, clear meta descriptions, and sitelink structure that projects maturity. On the page, showcase certifications, attestations, customer evidence, and third-party validation. Make legal, compliance, and security documentation easy to find. Treat E-E-A-T as table stakes, not a differentiator.
What should your keyword strategy prioritize?
Many teams start with product keywords, then wonder why traffic does not convert. A better framework orders targets by intent and risk posture. Build a core of stable solution, architecture, and framework keywords. Layer problem and detection queries that reflect attacker behavior. Add compliance and public sector terminology that aligns with procurement language. Reserve product and feature queries for conversion hubs. SEO for Cybersecurity gains leverage when it connects these layers through consistent internal linking and clear navigation.
- Solution layer: zero trust network access, identity threat detection, data security posture management.
- Problem layer: lateral movement, privilege escalation, ransomware dwell time.
- Compliance layer: FedRAMP, CMMC, SOC 2, industry-specific mandates.
- Conversion layer: pricing, demos, integrations, supported platforms.
Use query clustering to group related intents. Then assign content types to each cluster. Guides and frameworks for solution queries, deep dives for problems, comparison pages for competitive evaluations, and implementation pages for conversions. This is where SEO for Cybersecurity aligns with buyer enablement rather than just rankings.
How do you build topical authority without oversharing?
Security teams worry that detailed content may help adversaries. The answer is to publish guidance that informs defenders without operationalizing attacks. Focus on methodologies, detection logic concepts, kill chain mappings, and outcome-centric architecture patterns. Create a threat research cadence that deconstructs incidents and maps them to your controls. For SEO for Cybersecurity, this approach delivers depth, not sensitive configuration details. Pair each technical piece with executive summaries that translate risk into business impact and governance.
Editorial governance matters. Establish redlines for sensitive material, review flows with product security and legal, and a process to update posts as the situation changes. This protects brand integrity while compounding authority around your chosen pillars.
How can you win federal and regulated sector searches?
Public sector buyers search differently. They use acquisition terms, contract vehicles, and compliance phrases. To capture this intent, align taxonomy and content to federal frameworks, mission outcomes, and procurement language. Build specific landing pages for FedRAMP status, Authority to Operate pathways, IL levels, and agency use cases. SEO for Cybersecurity should also address state and local standards, critical infrastructure designations, and sector-specific directives. Pair these with case narratives and measurable outcomes appropriate for clearance and disclosure policies.
If federal is a priority, align your plan with proven public sector digital marketing techniques. Integrate FAQs that answer common acquisition questions, publish documentation indexes for contracting officers, and make accessibility compliance explicit. This meets both human and machine expectations for clarity.
What on-page fundamentals matter most right now?
Search engines reward pages that answer questions completely, load quickly, and demonstrate clarity. For SEO for Cybersecurity, emphasize scannability and precision. Use concise H1s and H2s that mirror query language. Open with a plain-language definition and a verdict, then move to architectural context, selection criteria, and next steps. Include schema where relevant, especially FAQPage, Product, Organization, and HowTo for procedural content. Maintain a living glossary for acronyms and standards. Ensure documentation, uptime, and trust center links are one click away for validation.
Performance is non-negotiable. Buyers will not tolerate heavy animations or scripts that slow key pages. Optimize Core Web Vitals without sacrificing brand. Security audiences appreciate speed, clarity, and control more than motion design. That principle alone can lift conversion rates from organic.
How do you earn high-authority links in a risk-averse ecosystem?
Security publications and analysts prefer data-rich, methodology-driven references. Invest in original research, benchmark reports, and tooling that the community finds useful. Host calculative models for risk quantification, maturity assessments, or cost of breach estimates. For SEO for Cybersecurity, this type of asset attracts citations from media, academia, and government. Pair it with a disciplined digital PR program that respects disclosure norms and coordinates with incident response timelines.
If you need the right mix of content, PR, and search orchestration, partner with a specialized cybersecurity marketing agency. Integrated planning ensures your research earns credible coverage and that coverage consolidates authority to the pages that drive pipeline.
Where does content gating help or hurt SEO for Cybersecurity?
Gated content captures known demand. Ungated content builds new demand and authority. The right balance depends on objective and audience. As a rule, ungate executive primers, architectural frameworks, product comparison pages, and implementation guides. Gate analyst-caliber reports, proprietary benchmarks, and calculators that require data inputs, but always provide an ungated summary page with key findings. SEO for Cybersecurity benefits when the summary ranks and the gated asset converts.
Be transparent about data use and privacy. Include a shortform option for government or regulated users who cannot share detailed information. Respect for process reduces form abandonment and builds trust with high-stakes buyers.
How should product and category pages be structured?
Category pages explain problems and solution patterns. Product pages prove fit. For SEO for Cybersecurity, each category page should own a buyer narrative: definition, why it matters now, how to evaluate, selection criteria, and measurable outcomes. Link to deep dives, customer stories, and a comparison to adjacent categories. On product pages, lead with validated use cases, control mappings, integrations, operating environment, and performance at scale. Include a frictionless path to testing, including demo videos, sandbox access, and deployment guides.
Cross-linking between categories and products should be deliberate. Search engines and buyers infer clarity when these relationships are consistent. Avoid orphaned documentation. Bring docs, trust center, and integration directories into the same architecture so SEO for Cybersecurity signals reinforce each other.
How do you align SEO with sales engineering and analyst relations?
Security purchases hinge on validation. Sales engineers, solution architects, and analysts function as trust amplifiers. Build a shared content backlog that captures the most common objections, RFP criteria, and proof points raised in technical evaluations. Then turn these patterns into public answers. For SEO for Cybersecurity, this creates high-intent content that maps directly to how deals advance, not just how pages rank. Coordinate publication calendars with analyst briefings so terminologies match the waves and market guides that shape buyer vocabulary.
Instrument every key page with self-qualifying paths. Offer options to talk to an expert, run a guided assessment, or explore a lab environment. Attach measurement to each outcome so marketing and sales share a single view of contribution to pipeline.
What metrics should executives track beyond traffic?
Pageviews do not earn renewals. Executive dashboards must show how search contributes to revenue, influence, and market leadership. For SEO for Cybersecurity, prioritize:
- Share of voice across target clusters and competitive benchmarks.
- Coverage of critical topics by funnel stage, mapped to win rates.
- Assisted and direct pipeline from organic sessions at the account level.
- Content velocity and refresh rate on priority pages.
- Quality signals such as engagement depth, documentation downloads, and trust center interactions.
Link dashboards to your revenue operations model so attribution, velocity, and conversion logic are credible to finance and the board. Treat rankings as leading indicators, not the goal. The goal of SEO for Cybersecurity is qualified demand at sustainable CAC, with content that compresses due diligence time.
What does a pragmatic 18-month roadmap look like?
An effective plan moves in phases, each with clear exit criteria. Month 0 to 3 focuses on technical foundations, IA redesign, and a prioritized content backlog. Month 4 to 9 builds authoritative category and solution hubs, launches research assets, and scales digital PR. Month 10 to 18 optimizes conversion paths, expands into adjacent topics, and operationalizes refresh cadences. Throughout, maintain a rolling threat-to-solution mapping process so current events continuously connect to evergreen content. SEO for Cybersecurity succeeds when cadence beats chaos.
For a model of integrated planning, review Bluetext’s approach to search engine optimization and how strategy, content, design, and media reinforcement come together. The right orchestration compresses timelines and compounds authority.
How do you resource the program without overextending SMEs?
Subject matter experts are essential but scarce. Protect their time by codifying interview playbooks, creating reusable outlines by topic type, and enabling iterative reviews rather than ground-up rewrites. For SEO for Cybersecurity, pair a senior editor with each pillar to maintain voice and accuracy. Build a content ops rhythm that batches SME reviews and aligns with release trains. This reduces cycle time and preserves technical integrity.
Augment SMEs with research analysts and technical writers who understand ATT&CK, NIST, and cloud shared responsibility models. The combination yields content that is both discoverable and defensible, which is the core advantage in cybersecurity search.
Case-in-point outcomes you can expect
Teams that execute this model typically see faster growth in qualified organic sessions than in raw traffic. Branded search expands as category leadership takes hold. Comparison and evaluation pages become top converters. Earned media citations concentrate on research assets, lifting the authority of entire hubs. For enterprise or public sector pursuits, SEO for Cybersecurity improves influence on multi-threaded deals as procurement teams validate capabilities through ungated content and documentation.
The second-order effect is strategic. When your definitions and selection criteria rank, you shape how buyers frame the problem. That influence ripples into analyst reports, partner narratives, and ultimately, shortlists. This is why leadership treats search as a market-making function, not just a demand capture channel.
Common pitfalls to avoid
Several predictable mistakes slow or stall programs in this sector. Avoid them to keep momentum and credibility intact.
- Chasing news over narrative. Trend posts without a connection to stable solution hubs do not compound authority.
- Gating everything. If buyers cannot verify claims without a form, they will bounce to competitors.
- Bloated pages. Security audiences want fast answers and clear architecture, not dense prose.
- Disconnected docs. Trust center, compliance, and integration content should live in the same navigational system.
- Ignoring B2G language. Public sector searches follow acquisition conventions that require dedicated content.
- Underinvesting in PR. SEO for Cybersecurity needs authoritative links that usually come from research-driven storytelling.
How Bluetext accelerates results for cybersecurity leaders
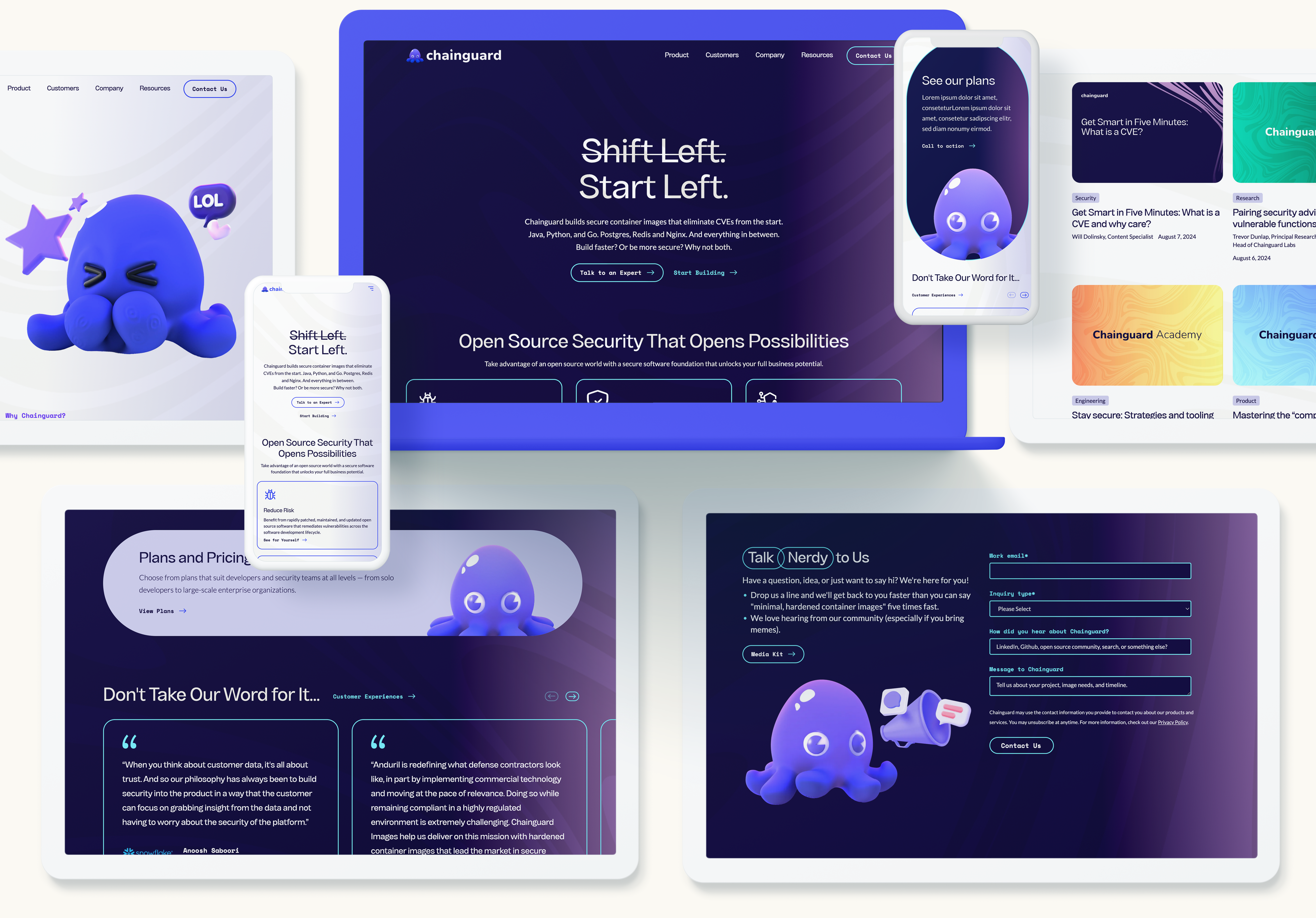
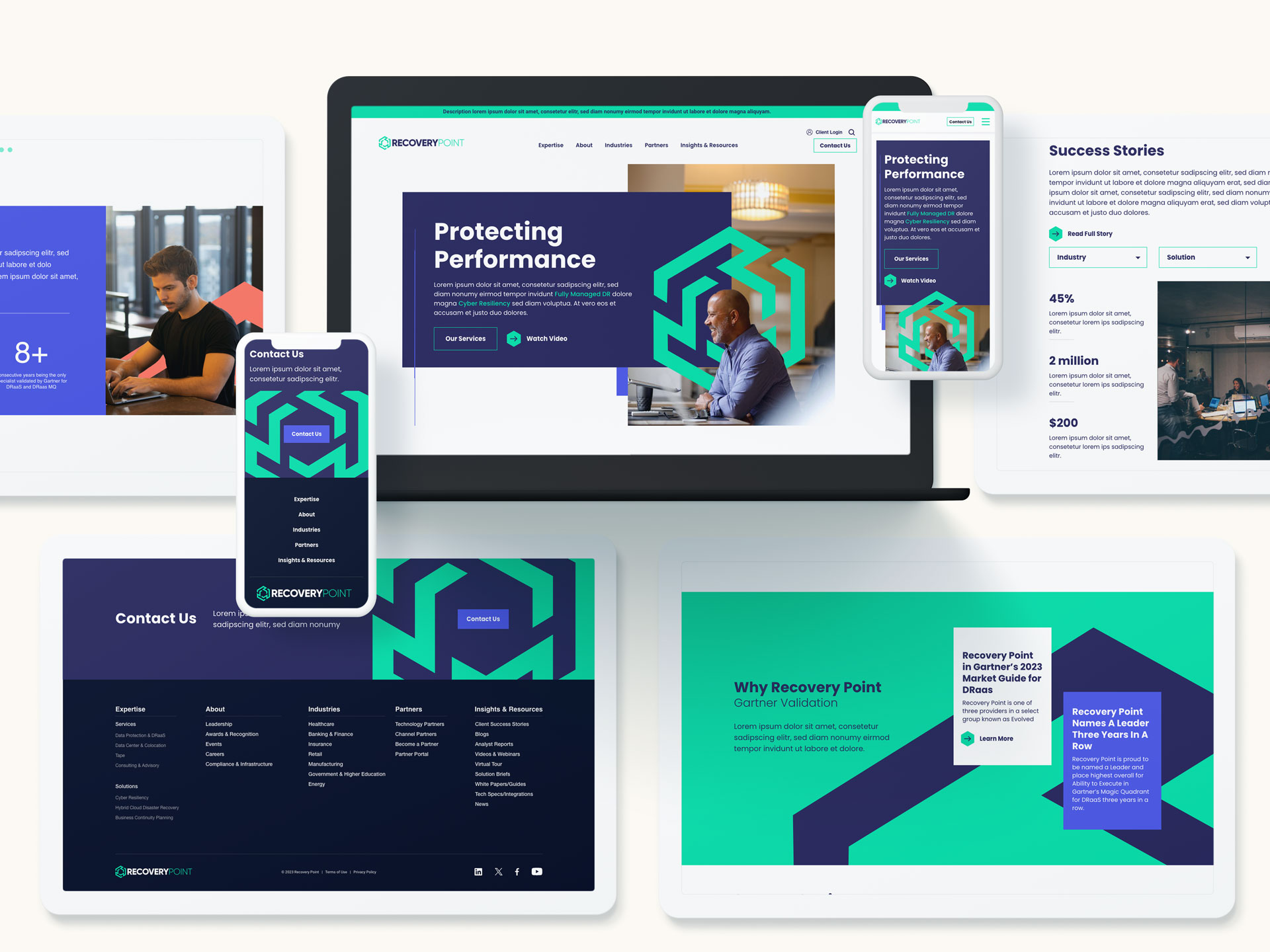
Bluetext has helped growth-stage and enterprise security brands define categories, clarify architectures, and win high-intent searches that move pipeline. Our integrated teams pair positioning and message architecture with technical content, UX, digital PR, and analytics. We architect programs so executive stakeholders can see contribution to revenue and brand leadership, not just traffic. Explore our work in cybersecurity for examples of narrative clarity, design systems, and campaign orchestration built for complex buyer journeys.
This sector demands a partner that knows how security leaders think and how search engines evaluate expertise. When you are ready to transform how the market discovers, understands, and trusts your solutions, contact Bluetext. If you need a broader integrated approach across brand and campaigns, our cybersecurity marketing capability and public sector digital marketing expertise can support every step of the journey. We will build an SEO for Cybersecurity program that compounds authority, reduces acquisition costs, and creates a durable advantage in the moments that matter.
Prefer listening over reading? Check out the podcast version of this blog below and enjoy insights on the go!
Security teams cannot defend what they cannot see, and the same truth applies to marketing. If your solutions, guidance, or research are invisible in search, the buyers who need you most will never find you. SEO for Cybersecurity aligns your brand, content, and technical infrastructure with the way CISOs, SOC leaders, procurement officers, and researchers actually search during critical moments. Done well, it increases qualified demand, compresses sales cycles, and strengthens digital trust at the precise moments that shape the outcome of a deal or crisis. For modern marketing leaders, SEO is not a channel to check off a list. It is a strategic capability that directly supports pipeline resilience and brand credibility in a volatile threat landscape.
What is SEO, and why does it matter now?
SEO focuses on the unique needs, search behaviors, and risk thresholds of security decision-makers. It elevates content that answers high-stakes questions across prevention, detection, and response. When a ransomware incident hits and a buyer searches for immediate help, the cybersecurity providers who have invested in SEO will appear with credible guidance and clear actions. That visibility translates to trust, and trust becomes a new business conversation. In B2G, where procurement rigor and compliance considerations are extensive, the right search visibility shortens discovery and validates a vendor’s authority early.
The cybersecurity market has matured beyond vanity keywords. Today, SEO prioritizes the intersection of intent, expertise, and speed. Executive buyers search differently from practitioners. Federal audiences search differently from enterprise teams. Search results pages have also shifted to favor authoritative answers and structured information, not just blogs with superficial coverage. The companies winning organic share are those that bring deep expertise to their content, reinforce it with technical excellence, and maintain rapid publishing cadences for emerging threats.
How should cybersecurity brands structure an intent-led content strategy?
The foundation of SEO is a content model built around buyer intent. Map topics to real scenarios and decision stages. Example categories include executive explainers on zero trust architecture, practitioner deep dives on SIEM tuning or EDR comparisons, and emergency guides for incident response. Every topic should have a clear purpose, a defined target persona, and an obvious next step.
- Define evergreen pillars: security operations maturity, vulnerability management, identity security, cloud posture, and compliance frameworks. Use these as permanent hubs for your authority.
- Create fast-turn clusters: pages for new CVEs, ransomware variants, and supply chain vulnerabilities. The brands that operationalize rapid publishing are the brands buyers bookmark.
- Build B2G tracks: content tailored to procurement workflows, ATO timelines, FedRAMP considerations, and interagency collaboration. These tracks support SEO for Cybersecurity while acknowledging public sector constraints.
Format matters. Technical evaluators favor detailed comparisons, architecture diagrams, and deployment runbooks. Executives want concise risk framing, total cost narratives, and case studies that show time to value. Both groups respond to content that is skimmable, accurate, and transparent. Successful SEO balances depth with clarity and uses structured elements such as checklists and step-by-step playbooks to satisfy search intent quickly.
What technical SEO improvements make the biggest impact for cyber brands?
Security audiences have low patience for slow or unreliable websites. Core Web Vitals, clean architecture, and robust internationalization are table stakes. Start with a streamlined site taxonomy that reflects how buyers navigate from high-level strategy to solution detail. Use internal linking to guide movement between related topics and to surface high-intent pages. Strong information architecture makes SEO in the cybersecurity industry more resilient as you scale content across products and markets.
Implement structured data wherever it informs the searcher. Product, FAQ, How To, and Article schema can improve discoverability and sitelink coverage. For vulnerability advisories and CVE documentation, standardized labeling and precise metadata are essential. Accelerate indexing with clear sitemaps and a publishing process optimized for speed and version control. If you run status or incident hubs, apply thoughtful indexation rules so that public communications are discoverable while sensitive operational pages remain controlled.
Security buyers often prefer browsing on locked-down devices or via mobile during off-hours. Mobile responsiveness, reliable HTTPS configuration, and lightweight code become competitive advantages. Combine technical cleanliness with measured pacing of scripts and trackers. That improves user experience and reduces the likelihood of false positives with endpoint protections. The end result is a technical foundation that supports SEO without introducing friction.
How do credibility, E-E-A-T, and digital PR reinforce search authority?
Cybersecurity is a YMYL category where expertise and trust are non-negotiable. Elevate named authors with verifiable credentials. Publish real research with original data, not recycled commentary. Provide transparent editorial standards and update logs on time-sensitive content. When you demonstrate experience and authority, search engines and buyers reward you. This is the essence of SEO in high-stakes categories.
Your backlink strategy should mirror the industry’s trust graph. Prioritize mentions and citations from respected analyst outlets, academic communities, standards bodies, and industry associations. Avoid low-quality link schemes that risk reputational damage. Run digital PR around responsible vulnerability disclosures, joint research with partners, and policy commentary that adds genuine value. As these signals accumulate, they compound the impact of SEO and protect your brand during crises.
What role does thought leadership play in demand generation?
Effective thought leadership turns organic demand into pipeline. Long-form guides on NIST CSF alignment, zero trust implementation roadmaps, and MDR vs. XDR decision frameworks meet buyers where they are. Pair these assets with calculators that quantify risk reduction or SOC efficiency gains. Package learnings into short executive briefs for the C-suite and deeper technical documentation for practitioners. When thought leadership drives clarity, it accelerates qualified conversations and strengthens SEO across priority topics.
How do B2G requirements change the SEO approach?
Public sector buyers face distinct procurement steps, compliance gates, and budget rhythms. Content must speak to these realities: authority to operate, cloud security posture, supply chain integrity, and vendor risk management. Create pages that align with key contract vehicles, timelines, and compliance milestones. Above all, use precise language and avoid marketing abstractions. Clear alignment to mission outcomes increases trust and drives performance in SEO for federal and state audiences.
Localization often helps. When targeting specific agencies or regions, reflect their terminology, use cases, and regulatory references. Build structured pages that address common questions from contracting officers and technical evaluators. Offer credible proof points: implementation timelines, integration patterns with government tech stacks, and support models. This directly supports SEO by reducing ambiguity and highlighting measurable value.
How can SEO mitigate crisis risk and support incident response?
During a security event, search becomes a truth-seeking channel. Plan for “brand + breach” and “brand + vulnerability” scenarios with prebuilt playbooks. Create a response hub that centralizes verified updates, FAQs, and remediation steps. Use canonical signals to avoid outdated information outranking current guidance. Coordinate PR, legal, security, and marketing teams to publish quickly and coherently. Placing accurate, helpful content in the SERP is a tangible way SEO defends reputation when it matters most.
What metrics prove value to the C-suite?
Executives need proof that organic performance drives business outcomes. Move beyond traffic and rank positions. Track assisted revenue, pipeline influence, share of search in target categories, and conversion quality by intent. Measure how often buyers who entered via organic convert to sales-qualified opportunities compared to paid channels. These indicators make the ROI case for SEO for Cybersecurity with clarity and credibility.
Layer in operational diagnostics: indexing efficiency, time to publish for critical content, and visibility for executive queries like “best zero trust vendors” or “incident response retainer.” Monitor brand SERP health, including sitelinks, knowledge panels, and presence of third-party reviews. Analyze log files to identify crawl waste and prioritize technical fixes. This discipline ensures SEO remains a durable growth engine rather than a reactive project.
How do you operationalize SEO for complex security portfolios?
Organize teams around topics, not just products. Establish a governance model with editorial standards, SME review cycles, and an always-on calendar for emerging threats. Build cross-functional rituals among product marketing, research, comms, and demand gen. Equip the team with templates for comparison pages, advisory posts, implementation guides, and FAQs. Systematizing production improves speed and consistency, which directly strengthens SEO at scale.
Finally, connect organic insights to broader go-to-market motions. Feed search intent data into ABM lists, paid search negatives, webinar themes, and sales enablement. Use organic performance to inform product naming, messaging pillars, and positioning tests. When SEO is integrated with brand, creative, and campaigns, the entire program becomes greater than the sum of its parts.
Move from visibility to velocity with Bluetext
Security markets reward clarity, speed, and credibility. That is exactly what a modern, integrated program delivers when SEO is built into your brand, content, and digital infrastructure. If you are ready to capture high-intent demand, strengthen your authority with decision-makers, and operationalize fast, reliable publishing, Bluetext can help. Contact our team to elevate your strategy, sharpen your positioning, and launch campaigns that turn search into sustained growth.
The recent Labor Day continued to shine a spotlight on an ongoing problem brought on by COVID-19: The Great Job Exodus of 2021. According to Microsoft’s 2021 Work Trend Index, 40% of the global workforce is considering leaving their employer this year. While many companies adopted more flexible work policies to adapt to the pandemic — with some being here to stay permanently — employees are continuing to experience burnout and businesses are seeing employees flee by the dozens.
Social media platforms such as LinkedIn have exposed a high percentage of PR and marketing professionals leaving their positions no matter the industry or tenure. Businesses large and small are struggling to fill key marcomms positions — specifically those in the mid and senior roles. And who can blame them when they’ve been working for 5 years or more, exhaustedly grinding away with a pandemic raging?
Finding and retaining top in-house talent can negatively impact the ability of marcomms teams to execute. The absence of senior leaders can make it difficult to provide the C-Suite with the strategy and ideas essential to growing the business. Additionally, if you can’t fully staff the team with junior and mid-level professionals, it can bog down more experienced marcoms professionals in tactical, rather than strategic, work.
The current conditions make a strong argument to fill the gap with a tech PR agency, like Bluetext. Leaning on an agency partner for additional services and support can alleviate some of that workload and bring fresh ideas and perspectives to your business. However, picking an agency is no easy task. Businesses need to find trusted advisors and agencies that will be an extension of the company; trustworthy firms that understand your business, products, and values. So, how do you pick the right partner to fill these gaps? Let’s dive in!
Benefits of an Agency Partner vs. In-House Staff
While both options have their benefits, deciding on an agency or in-house staff really depends on what your business is looking for, and it can depend on a variety of factors. While an in-house employee will, over time, know the ins and outs of your brand, it is rare to find an in-house marketer who is adept at all aspects of digital marketing. And if you do find someone who knows all aspects of digital marketing, it could be an overwhelming experience for them and may impact employee retention.
With an agency, you gain the benefit of a team of individuals with complementary skills who already work well together. An agency can also bring a fresh perspective, based on work with others in your industry, and even competitors. In-house marcomm professionals are at times so close to the brand it can lead to overly subjective decisions.
As for media relations, a public relations agency will have years and years of experience in multiple industries. Their media relations roots are continuously growing as they’re passed from client team to client team. Agencies have a plethora of relationships with media that are nurtured continuously from client’s both past and present. In general, agencies have a better understanding of media, industry trends, and the ever-changing media landscape and can easily adapt a strategy to meet the needs of their clients.

What to Ask Yourself when Finding an Agency
1. What are my goals?
This is a no-brainer! What are your marketing goals? The answer will determine which agency is right for you, what resources an agency should have, and more. Does this agency have enough experience and resources to help you achieve core objectives, does it have a presence in your target market or will you be able to build relationships with media through this agency? All of these questions are important to ask when it comes to choosing the correct agency partner.
2. Does my staff have the required resources and skills needed to achieve said goals?
By understanding which marketing tactics your business needs and the resources and skill level needed to do it, you’ll be able to find the right agency for your business. If you’re looking for more comprehensive marketing services none of your in-house roles can accomplish, be sure to pick an agency that has a diverse skill set to cover your bases. As a fully integrated marketing agency, Bluetext has a variety of services we offer to our clients that include messaging, branding, website design and development, go-to-market campaign strategy, public relations, social media, and so much more.
3. What value will I get for the cost?
When evaluating an agency, the math needs to be done to compute the true cost of the output. With an agency, you get the support of an entire team rather than just one person, therefore, getting more for less.
4. What is my budget?
By determining your budget, you can decide how much you can afford to invest in marketing which will dictate how much work your agency will take on. Sometimes what you can afford is too little to drive real results with one agency but can work for another.
Once you’ve asked yourself what your goals, budget, staffing needs, and skillset needs are, be sure to contact Bluetext to learn how our B2B tech PR team can help you fill any in-house skills gaps you are facing.
Given the speed at which news is consumed today, timing is everything. Latching onto a rapidly developing news cycle is a great way to gain visibility for your brand, establish thought leadership on a topic and build relationships with reporters. Rapid response, or newsjacking, opportunities are when brands capitalize on breaking news to provide relevant commentary on the story while drawing attention to their own content.

As brand storytellers, we’re scanning the news daily for what’s happening in the industry, what brands are standing out, how our clients are showing up and more. Thus, implementing a rapid response strategy during your daily news scans is easy, time-efficient and can be very fruitful. However, there are a few things to be wary of, including sensitivities around the news, reaction time and offering valuable insights.
Read the Room
Not every breaking news story needs commentary. Consider the sensitivities around the developing story, read the room and evaluate if a comms strategy is necessary around this cycle. If yes, then designate who your spokesperson will be and develop your commentary.
Amid tragedy at a global scale, like social unrest, natural disasters or pandemic, it is best advised to redirect external communications to focus on internal messaging and making sure employees feel supported. Exploiting tragedy and proactively telling a reporter how a company’s software product might have altered a tragic situation can be perceived as insensitive and will put your brand in a negative light.
A prime newsjacking market is cybersecurity. There are countless hacks that offer opportunities for cybersecurity firms to comment on topics like how the hack occurred, how that kind of hack or bad actor will evolve throughout the year and beyond, background on the hack or bad actor, what cybersecurity protocols can be implemented to prevent the hack from occurring again and more. But the noisier the market (and there are thousands of cybersecurity vendors with something to say), the more you will have to carve out a defined lane and message that reporters will find of value.
Timing Is Crucial
News comes and goes fast. Rapid response opportunities work best when you’re the hare, not the tortoise. In your daily scans, once you see a trending piece or developing piece and think that news cycle will pick up, get ahead — reach out to your spokesperson, pick their brain about how the story will develop, compile their thoughts into a pitch and ship it off to relevant reporters. From there, wait for the story to develop and see if the reporter has any other questions.

Yes, and ?
While timing is crucial in rapid response opportunities, it isn’t everything. Messaging is just as important. It does help to be the first to comment, but other brands won’t be far behind, and if your messaging does not add value to the conversation, it will not be included. On top of that, given the opportunity is industry-wide, keep the commentary broadly applicable but nuanced enough to stand out. This is not the time to gush about your company and the latest products.
There is a time and place for everything. While we as communicators want to jump on as many opportunities as they come, we need to be cautious about the ever-changing news landscape, the sensitivities of the world and the reputational risk that comes with it.
To learn more about how Bluetext can improve your newsjacking processes and timing, contact us today.
Amidst all of the business uncertainty in 2020 due to COVID-19, one area that remained relatively stable was a healthy volume of M&A activity for government contractors and government IT service providers.
You would be hard-pressed to find a tech PR and marketing agency that has helped to support the number of successful M&A events in the public sector space as Bluetext. It’s a big reason government contractors and Federal IT providers – along with private equity firms – turn to us to develop B2G PR campaigns that are designed for this very purpose. Thirty-four times in fact, Bluetext clients have been acquired within 24 months of an engagement with our agency.
I recently put together an op-ed for Washington Technology with 5 key PR strategies for B2G firms to consider before, during, and after an M&A transaction event. You can find the article here.
To learn more about our work with B2G clients in the M&A arena and how we may be able to help you achieve your own M&A goals, contact us today.
Thank you for joining us for the Q1 2021 Bluetext Cybersecurity Summit. Exclusively open to CXO’s, our goal with this summit is to deliver a value-add platform to network in the C-Suite with businesses facing similar opportunities and challenges.
Topics:
We plan to discuss the following items:
- Technology Customer Investment Trends
- Technology Consolidation Trends
- 2021 Trends
Date/Time:
2:30pm-4:00pm EST
Thursday, January 28th, 2021
Where:
COMING SOON: A link will be distributed with a calendar invite to all invited.
Agenda:
- Welcome from Jason Siegel: 1 minute
- Welcome and Introduction from Moderator, Morgan Wright, SentinelOne: 3 minutes
- Introductions of each business by one of the representatives (2 minutes each): 15-20 minutes
- Five questions will be softballed out, each receiving 5-10 minutes of airtime.
Summit Specifics: Things to Know
- We will mute all microphones for audio clean-ness
- The raise hand functionality will be used to orderly unmute speakers
- A recording of this conversation will be archived so keep it clean, friends
Moderator
 Morgan Wright
Morgan Wright
Chief Security Advisor, SentinelOne
Morgan is an internationally recognized expert on cybersecurity strategy and cyberterrorism. He currently serves as a Senior Fellow at The Center for Digital Government, Chief Security Advisor for SentinelOne, and is the chief technology analyst for Fox News and Fox Business on cybersecurity, cyberterrorism, national security, and intelligence.
Companies in Attendance:
AffirmLogic
About: AffirmLogic’s Hyperion platform applies advanced Mathematical Behavioral Computation that enables security teams to detect, analyze, and defend against even the most insidious malware—including advanced persistent threats (APTs) and other sophisticated, potentially devastating forms of attack.
Invited:
Larry Roshfeld, Chief Executive Officer
ArdentMC
About: ArdentMC is a trusted provider for geospatial information, cloud migration, and DevOps in the federal, state, and local business spheres, delivering quality products and outstanding performance initiative to every client.
Invited:
Michael Matechak, Chief Strategy Officer
CI Security
About: CI Security provides Managed Detection and Response and Cybersecurity Consulting services to help their customers to be secure, compliant, and resilient against threats to the life-safety, life-sustaining, and quality-of-life systems and services they provide to customers and communities.
Invited:
Jake Milstein, Chief Marketing Officer
EnHalo
About:
EnHalo is a group of global companies under one brand that is locally engaged, while globally operated. EnHalo focuses on three business pillars: Reducing Risk through its cybersecurity offerings, Reducing Cost through digital transformation, and Increasing Revenue through automation.
Invited:
Chris Beard, US President
Carol Watson, Director, Sales & Operations
Illusive Networks
About: Illusive Networks, the leader in deception-based cybersecurity solutions, empowers security teams to preemptively harden their networks against advanced attackers, stop targeted attacks through early detection of lateral movement, and resolve incidents quickly.
Invited:
Claire Trimble, Chief Marketing Officer
Infinite Group (IGI)
About: IGI works with organizations on all levels of IT security. Its areas of practice include managed security, incident response, social engineering, physical & perimeter security, administrative security, and internal security.
Invited:
Andrew Hoyen, President & COO
Kryptowire
About: Kryptowire provides software assurance tools for mobile application developers, analysts, enterprises, and telecommunication carriers.
Invited:
Alex Lisle, Chief Technical Officer
Obrela Security Industries
About: Obrela Security Industries (OSI) provides enterprise-class professional and managed IS services to assess and manage information risk in complex enterprise environments.
Invited:
George Patsis, Chief Executive Officer
Phosphorus Cybersecurity
About: With a 7 year half-life for vulnerability patching, and infrequent, if ever, credential rotation, IoT is the softest target on the network today. Phosphorus automates remediation of the biggest vulnerabilities in IoT.
Invited:
Chris Rouland, Chief Executive Officer
Rebecca Rouland, Chief Financial Officer
Sertainty
About: Sertainty technology implements a proprietary zero-trust architecture by embedding actionable intelligence into data-files. Sertainty makes it possible for data to be self-aware, self-protecting, self-acting. This gives software developers, systems integrators and their end-users a better way to monetize valuable information, lower the cost of compliance and mitigate risk in real time.
Invited:
Rivers Nesler, VP, Communications & Legal Affairs
Securonix
About: Securonix delivers a next generation security analytics and operations management platform for the modern era of big data and advanced cyber threats.
Invited:
German Fabella, Creative Director
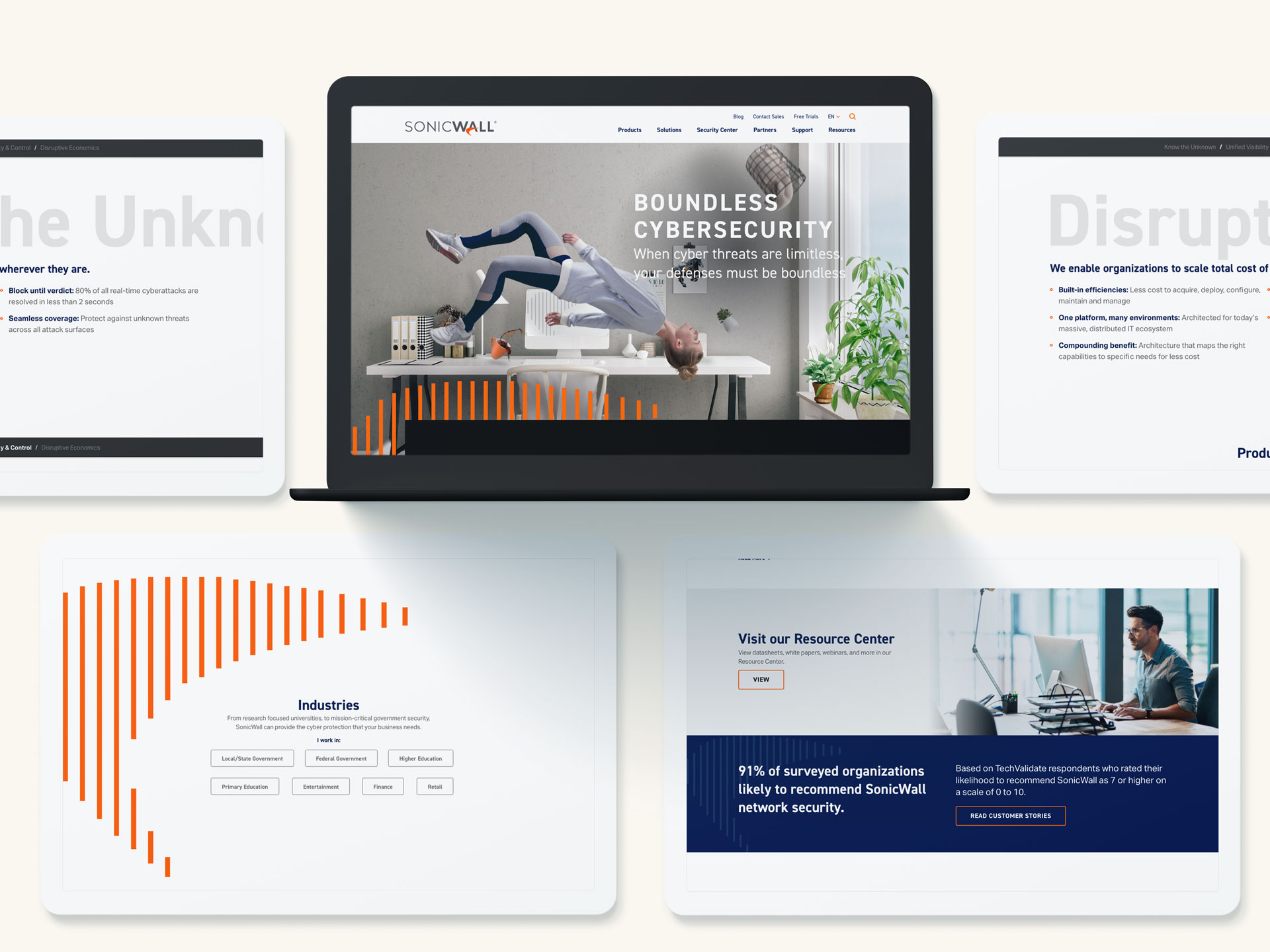
SonicWall
About: SonicWall Boundless Cybersecurity safeguards organizations with seamless protection that stops the most evasive cyberattacks across boundless exposure points and increasingly remote, mobile and cloud-enabled workforces.
Invited:
Geoff Blaine, Senior Vice President, Corporate Marketing
SpyCloud
About: SpyCloud is laser focused on preventing online fraud with our proactive solutions, which protect billions of employee and consumer accounts worldwide from account takeover.
Invited:
Company CXO’s
Stage2Security
About: Stage 2 Security is an Adversary Simulation, Protection, and Prevention company focused on building confidence in our clients’ IT systems.
Invited:
George McKenzie, Chief Executive Officer
Thank you for joining us for the Q4 2020 Bluetext Cybersecurity Summit. Exclusively open to CXO’s, our goal with this summit is to deliver a value-add platform to network in the C-Suite with businesses facing similar opportunities and challenges.
Topics:
We plan to discuss the following items:
- Technology Customer Investment Trends
- Technology Consolidation Trends
- MUCH MORE ….FILL IN SURVEY LINK BELOW
Date/Time:
COMING SOON: PLEASE FILL IN THIS SURVEY
Where:
COMING SOON: A link will be distributed with a calendar invite to all invited once the survey is done below.
Agenda:
- Welcome from Jason Siegel: 1 minute
- Introductions of each business by one of the representatives (2 minutes each): 15-20 minutes
- Five questions will be softballed out, each receiving 5-10 minutes of airtime.
Summit Specifics: Things to Know
- Jason will mute all microphones for audio clean-ness (something our 1st Presidential debate should have done)
- The raise hand functionality will be used to orderly unmute speakers
- A recording of this conversation will be archived so keep it clean, friends
Companies in Attendance:
AffirmLogic
About: AffirmLogic’s Hyperion platform applies advanced Mathematical Behavioral Computation that enables security teams to detect, analyze, and defend against even the most insidious malware—including advanced persistent threats (APTs) and other sophisticated, potentially devastating forms of attack.
Attending:
Larry Roshfeld, Chief Executive Officer
Bill Yarnoff, Chief Growth Officer
Infinite Group (IGI)
About: IGI works with organizations on all levels of IT security. Its areas of practice include managed security, incident response, social engineering, physical & perimeter security, administrative security, and internal security.
Attending:
Andrew Hoyen, President & COO
Phosphorus Cybersecurity
About: With a 7 year half-life for vulnerability patching, and infrequent, if ever, credential rotation, IoT is the softest target on the network today. Phosphorus automates remediation of the biggest vulnerabilities in IoT.
Attending:
Chris Rouland, Chief Executive Officer
Rebecca Rouland, Chief Financial Officer
Sertainty
About: Sertainty technology implements a proprietary zero-trust architecture by embedding actionable intelligence into data-files. Sertainty makes it possible for data to be self-aware, self-protecting, self-acting. This gives software developers, systems integrators and their end-users a better way to monetize valuable information, lower the cost of compliance and mitigate risk in real time.
Attending:
TBD
Trusona
About: Trusona is the pioneer and leader in password authentication. Stolen or weak passwords are responsible for over 80% of breaches, and Trusona’s mission is to thwart cybercrime by eliminating them from the user experience.
Attending:
Ori Eisen, Founder & Chief Executive Officer
Kevin Goldman, Chief Experience Officer
T2
About: T2™ manages large-scale technology projects for some of the most respected health systems and businesses in the United States.
Attending:
Kevin Torf, Managing Partner
Jim Rockenbach, Chief Strategy Officer
Verve Industrial Protection
About: Verve Industrial Protection’s mission is to protect the world’s critical infrastructure. For twenty-five years, Verve has helped its clients simplify and reduce the cost of building and maintaining secure, reliable, and compliant industrial control systems – DCS, PLC and SCADA.
Attending:
John Livingston, Chief Executive Officer
Cybersecurity has been a hot topic in recent news, and the threat of hackers and cyber-attacks has every industry on edge. The cybersecurity industry is booming in B2B and B2C markets, but so much media attention can be a double-edged sword. Consumers and businesses are tuning in for the latest updates, but the industry is crowded with voices. Cybersecurity firms must now pivot their attention toward marketing efforts to further differentiate their products and services from competitors. A fierce marketing strategy is a relatively new requisite in the cyber arena, leaving many experts turning to a top cybersecurity marketing agency for advice.
Bluetext’s Tactics to Tackle the Competitive Cybersecurity Landscape
Proper PR Prep
They’re called cyber specialists for a reason. Their expertise is in security and data protection, not press relations. While your firm may be at the top of their game in industry knowledge, nothing tanks credibility like a fumbled interview. Employing a marketing agency will ensure your firm is properly prepared to speak to the press by….
- Briefing Subject Matter Experts (SMEs) before interviews
- Planning an editorial calendar far in advance
- Putting a creative spin on trending news topics, even the negative ones
- Developing unique pitch angles
- Maintaining positive long-term relationships with reporters
To learn more about mastering the art of media relations, read Bluetext’s “4 Public Relations Tips and learn how Bluetext can help your brand’s media relations program.
Controlled Communication
Cybercrime can spark panic within a business of any size. Especially within retail, healthcare or financial industries protecting consumer’s sensitive data has become a top priority. Media attention can be both helpful and harmful, raising red flags but also spurring paranoia. This requires a communication strategy designed to simultaneously calm nerves and warn against potential threats. A third-party agency perspective will provide balance to ensure messaging sounds both competent and comprehensible to customers with minimal subject knowledge. A skilled cybersecurity marketing agency with PR services will craft the right messaging that walks the line between reassurance and realism.
As FireEye’s cybersecurity marketing agency, Bluetext developed a series of branded marketing materials to explain a complex suite of products. The new tagline “We Don’t Blink” helped communicate their brand promise in a nonthreatening manner.
Credibility Through Content Marketing
Trust is a key component of any company’s success. Positioning the firm as a reliable source of thought leadership will lead to more long term business growth. Gain credibility in the industry by establishing subject matter expertise.
Prove expertise to clients by regularly publishing case studies, white papers, and blog insights. To stand out against the noise in a crowded industry, velocity is critical. Plan ahead and develop a schedule with content variety. Consistently publish insights in an attractive and readable format to boost your SEO rank and put you miles ahead of competitors.
Regardless of industry focus, content is key. Any cybersecurity marketing agency will tell you having valuable and relevant content is necessary to establish digital authority and elevating a site’s SERP ranking. Housing content on your site may seem like a simple fix-all solution, however, it requires a plan and a bit of legwork to get off the ground. Read Bluetext’s advice for building the Foundation for an Effective Content Strategy that will maximize the cybersecurity marketing agency relationship so that content receives the active attention it needs.
Audience & Placement
Cybersecurity firms have a wide range of buyer personas, and it is important to recognize the unique needs of each. A common flaw of marketing strategies is putting all your eggs in one basket. Don’t let your marketing strategy fall flat with a two-dimensional approach. A marketing agency will ensure your efforts reach all intended audiences at every stage of the funnel.
Any agency will conduct thorough industry research and competitive analysis. Staying up to date and identifying the right trade shows and channels will put you ahead of competitors.
Every audience will have distinct needs and pressure points, a cybersecurity marketing agency will conduct market research and recommend tailored messaging. Bluetext was hired as Varonis’ cybersecurity marketing agency and developed a multi-faceted campaign, using performance and audience targeting to generate both brand awareness and leads. Read more on this cheeky cyber campaign.
Seriously Smart Branding
For many potential customers, your cybersecurity products and services may be a little over their heads. Therefore, their decision may lean on the affective factors. How your brand presents itself becomes critical. Be smart with your branding, think carefully about what tone, colors, and styles will best communicate your brand value. Your brand aesthetics may seem trivial, but do make neglect this step. Going too bright and vibrant in color palette runs the risk of your company not being taken seriously, but too toned down and your company will never stand out in a sea of the greyscale.
For some rebrand inspiration, check out how Bluetext revamped a hot cybersecurity startup, Finite State’s, visual identity and website. Finite State was able to communicate its value and relevance with a smart, modernized style to communicate their mission of clarity.

Bluetext is a top cybersecurity marketing agency, and we can prove it. Check out more of our cybersecurity marketing solutions.
In a recent post, we described the value of metrics-driven PR to ensure that revenue and lead-generation goals are a key focus of every public relations program. A metrics-driven PR program is even more valuable in the crowded marketplace of cybersecurity, where literally hundreds of start-ups and challenger brands are competing for the growing investments from government agencies, enterprise corporations, and businesses of every size struggling to figure out their cybersecurity defenses.
Dunbar Security is a company whose focus on metrics-driven PR was key to their marketing and sales strategy. Dunbar has been a leader in the security space for nearly a century. Its iconic red armored trucks are visible and instantly recognizable in cities around the country, still retaining a look of the 1930s in a modern wrapper. With a client base and brand that would be the envy of any services company, it decided to add a cybersecurity division to complement its physical security relationships and turned to Bluetext to design and execute its go-to-market strategy.
Bluetext helped launch its first product, the industry’s first open source active response platform. To achieve the goals Dunbar had set, Bluetext developed a program of announcements and nuts and bolts media outreach, combined with a thought leadership component to broaden its visibility into the cybersecurity marketplace.
After analyzing Dunbar’s initial brand footprint, it became clear that its name in physical security, while an important and key asset, would not in and of itself translate into a successful product launch. What was needed was to leverage that name as a way to separate itself from the pack of start-ups in the market – for potential customers, having a hundred-year history means not having to worry if the products and services would still be around in five years – as well as differentiating its open source platform from the proprietary offerings of competitors.
The Bluetext solution was to secure bylined articles in key vertical as well as business publications that primarily focus on the value of an open source solution for an active response while reinforcing the brand’s iconic history and longevity to subtly distance itself from other start-ups.
Bluetext, working with Dunbar’s executives and subject matter experts, crafted a series of bylined articles for vertical publications in the cyber arena as well as for other vertical markets that are regulated for which having a response platform like Dunbar’s can help them meet their legal and regulatory requirements, such as healthcare and financial services. Our team of public relations professionals used its expertise and relationships to place dozens of bylines and coverage articles to spread the Dunbar message far and wide.

Using cloud-based analytical tools to measure reach and scope as well as the share-of-voice of the program, Dunbar was able to achieve success in the market far more quickly than it had hoped for.
Learn how Bluetext can execute a metrics-driven PR program for your cybersecurity brand.
PR is not a sinking ship. It’s still an essential element in your marketing mix, especially in the crowded cybersecurity market. But is your PR program delivering the results you need to meet your revenue goals?
Let Bluetext do a free PR assessment to see if:
- Your outreach is delivering the results you need
- You are gaining ground in the market
- You’re getting the coverage that will drive your growth
Our Share of Voice assessment can let you know if you are hitting on all cylinders, or if your program needs a shot of high-test to get it in gear.
Click here to sign up for your FREE Cybersecurity PR Assessment!