Cyber threats are escalating in speed, scale, and sophistication, and the buying committee is expanding just as quickly. That reality raises the bar for marketing leaders in security. Winning requires relevance to CISOs, clarity for practitioners, and credibility with the board. Working with a cybersecurity marketing firm that understands both the technology and the enterprise sale is the difference between incremental results and market leadership. The following insights distill what leading firms are doing right so you can elevate strategy, accelerate pipeline, and strengthen brand authority.
What separates top cybersecurity marketing partners today
The best programs begin with an unflinching focus on the audience reality. A high-performing cybersecurity marketing firm internalizes how risk, compliance, architecture, and budget decisions are actually made. That means moving from feature-first messaging to evidence-led value narratives tied to operational outcomes like mean time to detect, dwell time reduction, and policy enforcement at scale. The firm’s job is to translate deep technical differentiation into stories that de-risk the decision for executives while equipping champions to drive consensus.
- Precision positioning rooted in market structure. Leading teams map competitors, substitutes, and adjacencies to carve out a defensible lane. A cybersecurity marketing firm then defines proof points and customer language that neutralize “good enough” alternatives.
- Program architecture aligned to the full buying committee. Security engineers want hands-on depth, finance leaders want cost predictability, and agencies require compliance clarity. A single plan must satisfy all without diluting the core idea.
- Relentless emphasis on credibility. Analyst relations, third-party validations, and quantified case studies are nonnegotiable. Trust is earned through substance and consistency.
How to craft a category narrative that buyers and analysts remember
A category narrative should make complex concepts immediately graspable. The goal is not to describe everything your platform does. The goal is to frame the problem and your point of view so succinctly that buyers can retell it inside their organizations. A seasoned cybersecurity marketing firm builds a narrative that aligns to pain, risk, and urgency across three tiers: macro threats, organizational impact, and role-based priorities. Done well, this narrative becomes the spine for campaigns, content, and sales tools.
Message architecture that scales across roles and channels
Start with a one-sentence promise that is anchored to a measurable outcome. Support it with three pillars that connect to platform capabilities and use cases. Translate each pillar into executive, practitioner, and partner proof points. A cybersecurity marketing firm then operationalizes the architecture across website pages, enablement decks, demo scripts, and PR talking points to maintain signal consistency while allowing depth where needed.
Which channels deliver pipeline in cybersecurity right now
Security buyers need a reason to reallocate constrained budgets. That means showing proof early, not after the gated form. ABM and field marketing work when they provide value in the first interaction. A high-performing cybersecurity marketing firm leans into technical content, peer validation, and tactical tools that help teams move an initiative forward this quarter. Events, communities, and intelligence briefings continue to convert when they are built around practitioner utility rather than product promotion.
Paid, owned, and earned tactics calibrated for intent
Start by using search and review platforms to harvest late-stage demand and direct it toward differentiated assets. Bolster credibility with earned media on real issues such as SaaS misconfigurations, software supply chain risks, and OT exposure. On owned channels, invest in explainers, frameworks, and sample policies that practitioners can deploy immediately. A cybersecurity marketing firm should unify these threads through a simple conversion path that prioritizes demos, proofs of concept, and risk assessments tied to business outcomes.
How to market security solutions to the public sector without risk
Public sector innovation cycles and buying processes differ meaningfully from enterprise norms. Compliance, certifications, and mission alignment matter as much as features. A strong cybersecurity marketing firm knows how to position capabilities for federal, state, and local requirements while respecting rules around procurement-sensitive claims. It is critical to balance thought leadership with precise language that aligns to contract vehicles, cybersecurity frameworks, and zero trust mandates.
Map campaign themes to mission outcomes such as resilience, continuity of operations, and cross-agency collaboration. Translate technical claims into acquisition-ready language that references control families and policy directives without overstepping. For B2G programs, align messaging to role-specific triggers for CIO, CISO, and program executive stakeholders. A cybersecurity marketing firm will also synchronize content release cycles with budget timelines and period-of-performance realities to improve win probabilities.
Proof builds trust: assets that convert security skeptics
Security decision makers have learned to ignore marketing claims. Instead, they respond to proof they can interrogate. Anchor campaigns in artifacts that reflect the rigor of your program and the maturity of your customers. This is where a cybersecurity marketing firm can unlock disproportionate impact by shifting your content mix toward evidence and practitioner utility.
- Quantified customer outcomes. Build repeatable case study formats with before-and-after metrics like time to remediate and alert fatigue reduction.
- Technical validation. Commission red team exercises or third-party pen tests and publish summarized findings with sufficient technical fidelity.
- Economic framing. Translate risk and controls into financial terms, making it easier for CFOs to support the plan.
- Hands-on experiences. Host guided labs and simulations that replicate real attack paths and defensive workflows.
Video and interactive experiences that reduce time to conviction
Video is often the fastest route to comprehension when products span identity, data, and network layers. Create short explainers that visualize control points along the kill chain, then drive to a deeper interactive lab. An expert cybersecurity marketing firm will sequence formats for progressive discovery, starting with an animated overview, bridging to a narrated demo, and culminating in a hands-on challenge. This structure compresses time to conviction for technical buyers and simplifies storytelling for executives.

Check out our video work with SecurityScorecard
Search, content, and AEO strategies for technical audiences
Search behavior in cybersecurity is fragmented across roles and stages, which demands precision. Rather than chasing generic keywords, define intent clusters that reflect real jobs to be done, such as exposure management, least privilege, or secure software development. An experienced cybersecurity marketing firm leverages content depth, structured data, and answer-engine optimization to win zero-click and long-tail moments while feeding ABM programs with context-rich leads.
- Answer real questions succinctly. Build FAQ-style hubs that resolve tactical needs like “how to implement just-in-time access” and “what is SBOM attestation.”
- Use structured data. Mark up definitions, product comparisons, and how-tos so answers surface quickly in rich results.
- Connect content to conversion. Each page should point to hands-on proof such as a lab, PoC, or calculator.
- Instrument relentlessly. Tie rankings to pipeline metrics to keep efforts focused on revenue.
Analytics is the glue. Mature teams bring together keyword universe mapping, competitive gap analysis, and content testing in one operating rhythm. For deeper audience intelligence and testing frameworks, explore Bluetext’s approach to research and analytics and how it informs channel and content decisions that drive measurable impact.
Metrics that matter to the CMO and the board
Security buyers reward rigor, and your measurement model should follow suit. Move beyond traffic and MQL counts to metrics the board values. A cybersecurity marketing firm will benchmark marketing-sourced pipeline, stage-by-stage conversion, velocity, and win-rate differentials for ABM accounts relative to the total addressable market. CAC payback, expansion rates, and multi-product attach are the trailing indicators that prove durable advantage. Align executive dashboards to these measures and ensure quarterly business reviews connect activities to revenue outcomes.
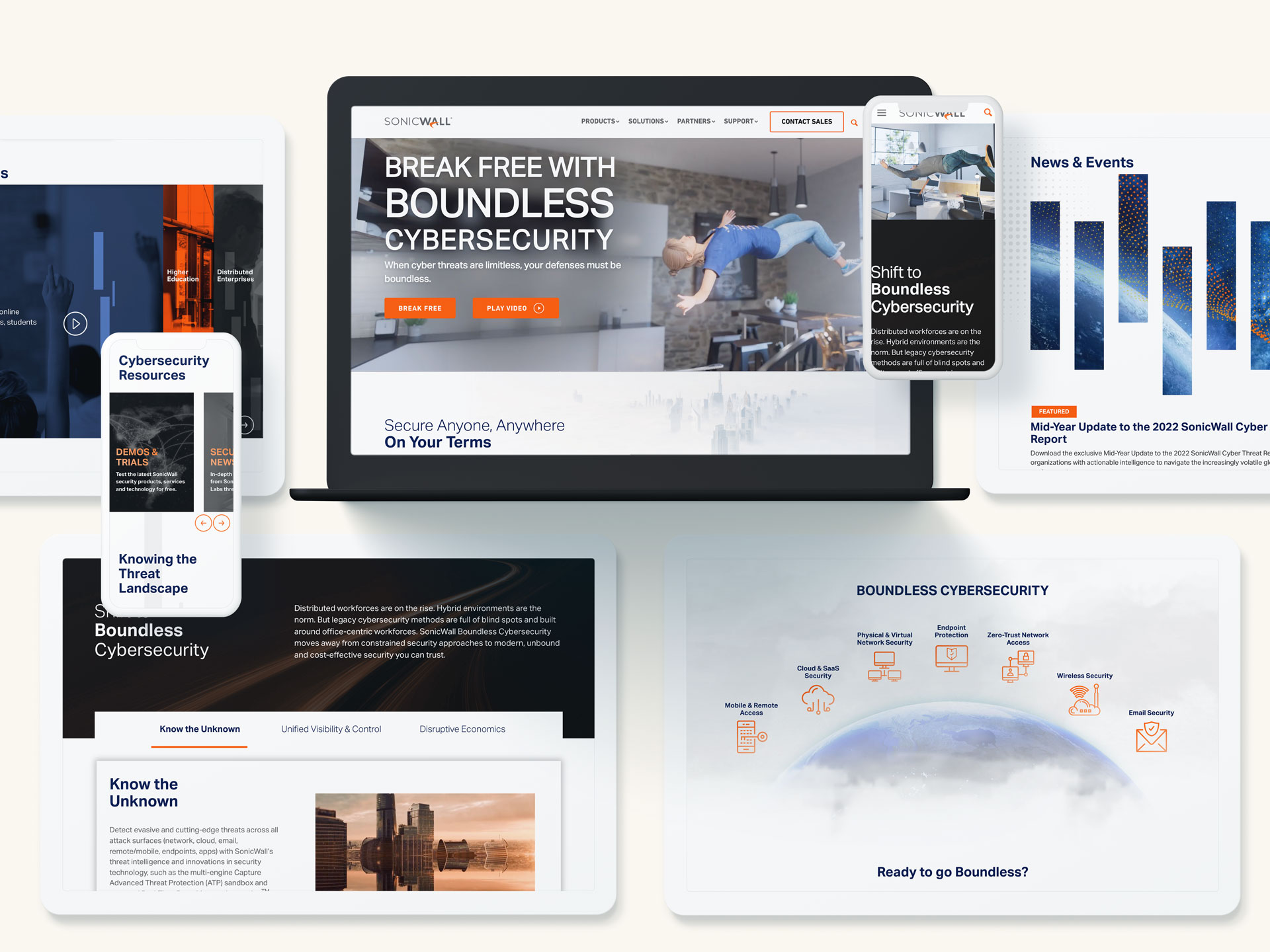
Dig into how we partnered with SonicWall
Selecting the right partner is a force multiplier. Look for a cybersecurity marketing firm that can work across both B2B and B2G motions with credibility. Evaluate their ability to simplify complex architectures without softening the technical truth. Review how they translate emerging trends like identity-first security, CNAPP, and software supply chain integrity into narratives that resonate with both analysts and end users. Ask to see measurement frameworks that tie positioning, content, media, and sales enablement together.
- Category experience. Your partner should have a portfolio that spans endpoint, cloud, identity, data, and OT security so they can anticipate objections and recommend accelerators.
- Brand-to-demand integration. A cybersecurity marketing firm must be equally fluent in brand strategy and demand generation, not one or the other.
- Speed and discipline. Cyber markets move quickly. You need agile sprints and editorial rigor to keep messages current and accurate.
- Public sector fluency. For sellers into government or contractors, ensure the team understands procurement sensitivities and accreditation pathways.
Finally, assess cultural fit. The ideal cybersecurity marketing firm will challenge assumptions, bring fresh creative energy, and embed with your sales and product leaders. They should complement your internal strengths and add the signal you do not have in-house, whether that is research depth, creative scale, or channel specialization.
Accelerating execution with an agency that knows the terrain
Turning strategy into market impact takes cross-functional alignment and polished execution. A specialized cybersecurity marketing agency brings planners, creatives, technologists, and media strategists to the same table so programs launch with momentum and sustain over time. Expect a planning cadence that translates category narrative into quarterly campaign themes, content roadmaps, and field plays. Insist on a creative process that makes complex ideas intuitive for buyers without sacrificing accuracy for speed.
When you evaluate creative, judge it on clarity, memorability, and technical integrity. Ask how the team will tailor core concepts to each route to market, from direct enterprise to channel and OEM relationships. A high-caliber cybersecurity marketing firm will build for modularity so assets repurpose across web, demand gen, events, and sales motions without creating inconsistency or rework.
From brand to proof: where Bluetext adds leverage
Bluetext has partnered with cybersecurity innovators across growth stages to build brands, launch categories, and drive measurable pipeline impact. Our teams synchronize research, positioning, visual identity, content strategy, and activation to deliver a coherent market presence. Explore examples of our work in cybersecurity to see how brand storytelling and technical depth come together in practice. When a cybersecurity marketing firm aligns narrative, creative, and channels, prospects understand your value faster and with more conviction.
We also prioritize the operational realities of enterprise and public sector buyers. From enablement kits that arm sales with objection handling to campaign architectures built for multi-quarter pursuits, the right cybersecurity marketing firm creates systems that scale. That includes structured governance for content accuracy, cross-functional review processes, and analytics models that attribute revenue appropriately across long cycles and complex deals.
A practical 90-day plan to elevate your program
To build momentum quickly, establish a 90-day sprint with clear outcomes and owners. A skilled cybersecurity marketing firm will help you focus on the moves that compound.
- Clarify the promise. Pressure test your one-sentence value proposition with customers and sales. Lock messaging, proof points, and a three-pillar framework.
- Fix the conversion path. Align top-performing pages, demos, and sales handoffs to a single storyline. Reduce friction to the two actions that best predict revenue.
- Publish proof. Release two quantified case studies and one technical validation asset. Promote across search, email, and community channels.
- Stand up intent harvesting. Launch a focused paid search program around your most defensible solution plays. Instrument from click to close.
- Enable the field. Deliver a concise enablement pack with talk tracks, ROI framing, and competitive traps. Train champions to retell the story faithfully.
Within this window, your teams should see higher demo acceptance rates, improved pipeline quality, and faster consensus among buying committees. These are the signals that your narrative, creative, and channel choices are resonating. A data-driven cybersecurity marketing firm will turn those early wins into an operating model that sustains results through the fiscal year.
Ready to elevate your cybersecurity narrative and pipeline
The stakes in security are too high for guesswork. Progress comes from message clarity, credible proof, and disciplined execution. If you are ready to sharpen positioning, strengthen creative, and launch programs that convert complex value into measurable growth, Bluetext can help. Begin the conversation today and see how an experienced cybersecurity marketing firm can turn ambition into market impact. To get started, review our approach, explore relevant case studies, and contact Bluetext to build a plan tailored to your objectives and timelines.